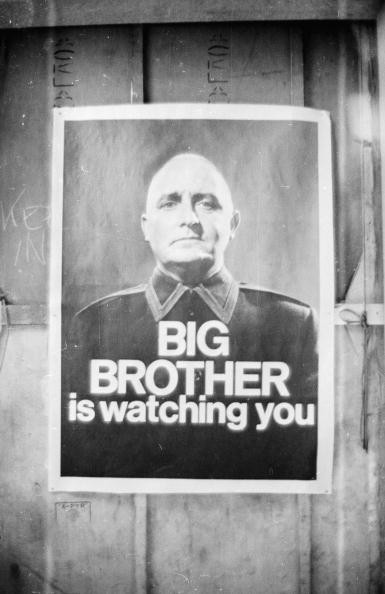
Big Brother is Watching: Policing of the Future is Here Today Says Morgan Marquis-Boire

"There was of course no way of knowing whether you were being watched at any given moment. How often, or on what system, the Thought Police plugged in on any individual wire was guesswork. It was even conceivable that they watched everybody all the time."
This is a quote from George Orwell's dystopian novel Ninteen Eighty-Four which was publised 65 years ago.
On Tuesday the UK government will fast-track legislation through parliament in order to safeguard the security of the country and its people - according to David Cameron at least.
The new legislation will force telecoms companies and internet service providers to retain users phone records, text messages and online activity for 12 months.
While there has been uproar in some quarters about the rushed nature of this legislation, the simple truth is that police forces and security agencies across the UK and beyond have much more powerful tools at their disposable which are capable of monitoring everything we do and say.
The capabilities of these tools may have been laid bare by Edward Snowden's revelations relating to governmental spying, but one former hacker has been looking at the people and companies behind these cyber-spying tools and how they are being abused by repressive regimes.
'(L)awful Intercept' tools
Having left Google after six years as a security researcher, Morgan Marquis-Boire is still settling into his new role as the director of security at First Look Media, where one of his primary objectives is to protect the very journalists who helped Edward Snowden publish his leaked documents.
However for the last few years it has been his research into what are known "lawful intercept" tools which has been his main focus.
Marquis-Boire's research into law enforcement, intelligence community malware - in particular the type which is sold on the pseudo-open market by companies like Hacking Team and UK-based Gamma International - has shone a light on the misuse of such cyber-weapons by repressive regimes to target activists and journalists.
His most recent research has laid bare the extent of the powers these tools put into the hands of law enforcement agencies.
Big Brother is watching you
Leaks show that a piece of software known as Remote Control System (RCS) allows governments to implant a piece of malware on your smartphone and take control of the device's microphone, camera, keyboard and even services like Facebook, WhatsApp and Skype.
RCS can infect iPhones even if they have not been jailbroken, and can take control of a smartphone's camera as well as the microphone to record everything a target is saying.
Tools like these are freely available to governments, intelligence agencies and even local police forces around he world, meaning that while the legislation which will be passed next week looks invasive, the truth is that if they really wanted to, agencies could already be monitoring your every move.
"Law enforcement of the future - today"
"This is the law enforcement of the future and actually the law enforcement of the now. [Hacking Team and Gamma International]'s customer base is expanding, this capability is something which you can see as being desirable to most law enforcement agencies," Marquis-Boire says when IBTimes UK meets him in London.
The dreadlocked former hacker wasn't surprised by the capability of this piece of software but what was interesting to him was "the amount of care that [Hacking Team] actually went to, to advise the operators of this gear, not to make mistakes, which I actually felt was in some ways a response to the amount of research that has been published on them."
Indeed because of the widespread media coverage of the research Marquis-Boire carried out in conjunction with the University of Toronto's Citizen Lab - added to the huge interest in the Snowden revelations - police forces and intelligence agencies from around the world are now looking at what is happening and wondering why they don't have these tools at their disposal.
The New Zealand native says that as part of his work he comes into contact with the "guys on the other side" who work for companies like Hacking Team or Gamma International and it turns out that rather than damaging these companies' balance sheets, Marquis-Boire's work in unmasking these sophisticated hacking tools has actually been a boon for them.
These tools are being used in countries around the world today - but not only in countries with repressive regimes but in developed western countries like the US, Australia and of course the UK.
Sunlight is said to be the best of disinfectants; electric light the most efficient policeman
The quote above is credited to American litigator Louis Brandeis and is one Marquis-Boire believes is relevant to the current situation with government surveillance:
"I don't think there is going to be more and more surveillance. I think one of the reasons we are in the mess we are in now is because this stuff has flourished in the darkness, in the artifices of the black state."
He says that the technology in use is "poorly understood, poorly regulated and poorly policed" and that while asking for ethics in the production of surveillance equipment is reasonable, he doesn't think companies like Hacking Team are "acting in a worse manner than anyone else who produces surveillance equipment."
Companies like Hacking Team are by their very nature secretive and unwilling to discuss what they do in public. These companies walk a fine line between what is legal and what is not, but speaking to IBTimes UK last year, Hacking Team's Eric Rabe pushed the official line:
"Hacking Team provides legal surveillance software to the law enforcement, intelligence communities and governments around the world. We sell exclusively to governments so no private person or business can buy this. This is a very effective product that allows law enforcement agencies to monitor the communications of people who may be under surveillance."
When is it OK?
And, at the end of the day, this is true. These companies create the products, they don't tell people what to do with them.
"A lot of the issue then lies with the fact that the implication is on the purchaser that they are going to use it properly, but we actually don't even know what properly looks like for this stuff," Marquis-Boire says.
This raises the question: When is it OK to use these powerful tools?
In the real world (as opposed to the cyber world) actions like wire-tapping, firing tear gas or deploying a riot squad are all police controls which need a conscious decision before being used.
When it comes to the use cyber-weapons, like those available to police forces nowadays, the way we use them and when we use them is not nearly as clear-cut.
"I think many members of the public actually have reasonable ideas of what they think is fair and effective policing, however I don't think many people have opinions on [use of spying tools] because they just don't know it's occurring," Marquis-Boire says.
"The police aren't spies"
While he doesn't think that there is "never a valid use for this type of technology" Marquis-Boire would "like us as a society to decide what that is".
It is one thing for spooks at the NSA or GCHQ to use sophisticated monitoring tools to track potential national security threats, but it is an entirely different thing for your local policeman to leverage the power of Hacking Team's software in order to find out who is stealing loaves of bread from outside the bakers at 3am on a Saturday morning.
"I think that there's a greater standard of transparency that [police forces] need to be beholden to, to the public. We don't actually expect spies to be transparent with us but the police aren't spies."
Understand privacy
The former hacker believes that we are currently in an transition period between realising we can do these things and "actually being adults with it."
He hopes this can "happen as quickly as possible so there is as little abuse of it as there can be."
We are "acting like people in our early 20s" with these tools, Marquis-Boire says but despite the abuse of these powers he has exposed, he is still optimistic about what the future holds.
"We have a generation of people who have actually grown up with this type of technology that I think understand privacy and how they expect to be able to act on the internet more intrinsically than we do."
© Copyright IBTimes 2025. All rights reserved.


























