Hackers are now using Facebook Messenger to spread 'advanced' malware code
The victim would be served with 'mult-platform' malware, Kaspersky Lab said.
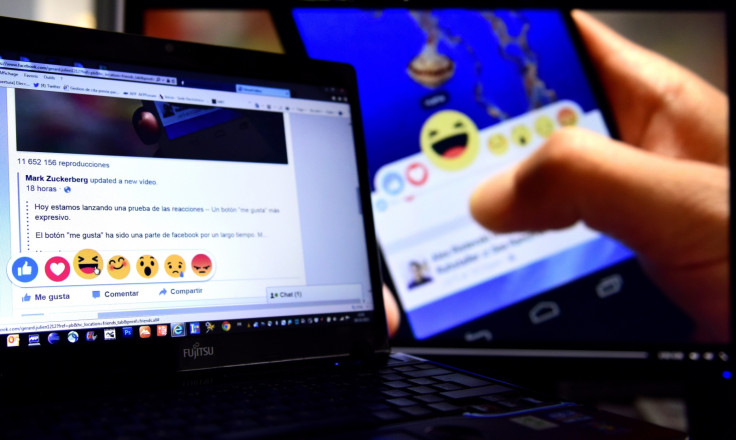
Hackers are now using Facebook Messenger to circulate malicious links in an attempt to trick unsuspecting victims into downloading various forms of adware.
It remains unclear how fast it is spreading – but experts believe it could be the result of stolen passwords, hijacked web browsers or a technique known as "clickjacking".
"This was spreading via Facebook Messenger, serving multi-platform malware/adware, using tons of domains to prevent tracking, and earn clicks. The code is advanced and obfuscated," said David Jacoby, an expert at cybersecurity firm Kaspersky Lab (24 August).
The Facebook message used typical social engineering tactics to trick users into clicking a link – meaning the content was designed to appear personalised.
In this instance, it came in the form of a short message with the victim's name, a shocked face emoji and a shortened Bit.ly link to a blurred out video.
Upon analysis, the link was pointed to a dynamic Google Doc landing page which was set up to look like a playable movie. When clicked, however, the malware would redirect the victim to a slew of websites which then analyse the computer's operation system and internet browser.
"This technique is not new and has a lot of names," Jacoby explained.
"I would like to describe it as a domain chain, basically just a lot of websites on different domains redirecting the user depending on some characteristics. It might be your language, geo location, browser information, operating system, installed plugins and cookies.
"By doing this, it basically moves your browser through a set of websites and, using tracking cookies, monitors your activity, displays certain ads for you and even social engineers you to click on links.
"We all know that clicking on unknown links is not something that's recommended, but through this technique they can basically force you to do so."
Interestingly, the websites the victim is redirected to would depend on what browser they were using. On Google Chrome, for example, the website was made to look identical to YouTube. It displayed a fake error message and urged the user to download a malicious extension.
On Mozilla Firefox and Apple Safari, the Kaspersky Lab researcher found that the website displayed a fake Flash update which, when clicked, would serve up an adware file.
"It has been a while since I saw these adware campaigns using Facebook, and it's pretty unique that it also uses Google Docs, with customised landing pages," Jacoby said.
"As far as I can see no actual malware (Trojans, exploits) are being downloaded but the people behind this are most likely making a lot of money in advertising and getting access to a lot of Facebook accounts. Please make sure that you don't click on these links."
© Copyright IBTimes 2025. All rights reserved.




















