John McAfee: Chinese government spies on aeroplane passengers through Silent Logging app

I recently had an epiphany: as bad as I might imagine the Western world's current ranking in the upcoming cyber world war, the reality is far worse. To test the hypothetical truth of my epiphany, I provided software, for Android smartphones, that would detect "man in the middle" attacks by devices that emulate legitimate cell phone towers, to hundreds of international travellers flying with four highly renowned airlines.
The software works by detecting anomalies in IMSI-catchers (International Mobile Subscriber Identity) that cannot be hidden by the manufacturers. IMSI-catchers are devices that emulate cell phone towers. They trick our smartphones into believing a cell tower suddenly appeared in close range and entices our phones to connect through it.
Once our smartphones have been sufficiently convinced, we are f****d. A man in the middle attack has just succeeded in controlling our communications. Once we have connected, the IMSI-catcher analyses our configuration and "pushes" the necessary software into our smartphones in order for some third party related to the IMSI catcher to take control.
"Any business person, diplomat or government employee, who has ever travelled on any of these four airlines, has forever after been wired by the Chinese government"
- John McAfee
But I am not here today to talk about stingrays. That discussion is coming and it will be intense. No, I am here today to talk about the Russians and the Chinese, and whether Western world nations will survive the undeclared cyber war which is upon us.
In every case where an international traveller with these four airlines attempted to connect to the onboard internet, a module was pushed to the connecting smartphone that surreptitiously turned on the 3G or 4G communications (without displaying the corresponding icon). From that point, an onboard IMSI-catcher attempted to connect to the phone. There was a 100% success rate.
The first order of business, after connecting, was to determine whether an Android app called Silent Logging was already present on the Android device. If not, it was pushed to the device. Silent Logging was then activated. For anyone unfamiliar with the app, it was created for the very purpose of spying on the owner of an Android smartphone.
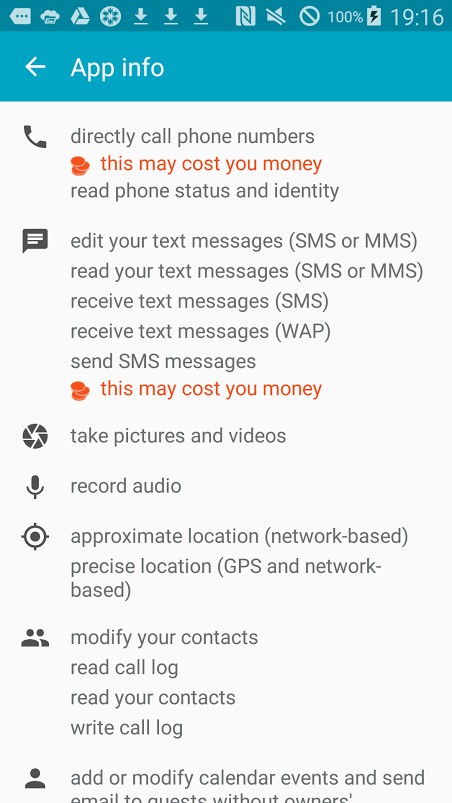
On the right is a screenshot of permissions asked by Silent Logging. This is just one of four pages of permissions asked by "Silent Logging".
After Silent Logging is activated, a spyware app is downloaded to the users' smartphone that utilises the Silent Logging app, unless the phone is "physically wiped" by the manufacturer, this software remains forever.
A factory reset (performed by the user), is intercepted by the spyware and the external signs of a factory reset are emulated by the spyware, therefore deceiving the owner into believing a factory reset had been perforned. The user is forever after under the control of the spyware app.
After the spyware app has been downloaded and connected, the owner's smartphone becomes a 24-hour-a-day spy device, reading all emails, text messages, recording audio and video and sending results to an IP address in Beijing.
Two things we can learn from this:
1. The TSA's misguided attempts to convince the American public that smartphones and computers emit signals that confuse aeroplane guidance systems are and have always been laughable and offensive to those of us American citizens who know better. One of the airlines encourages its users to turn their phones on when not on flights that connect with or pass through the US.
2. Any business person, diplomat or government employee who has ever travelled on any of these four airlines has forever after been wired by the Chinese government. Every email, text, word or action has been recorded for Chinese posterity.
I do not enjoy being the bearer of bad news. I am slandered, derided and s**t upon by every news outlets on the planet. Yet, how will we ever wake up if someone does not thrust the mirror of truth in front of our faces.
Who is John McAfee?
John McAfee is one of the most influential commentators on cybersecurity anywhere in the world. His new venture – Future Tense Central – focuses on security and personal privacy-related products. In September 2015, McAfee announced that he will be running for US president in 2016.
McAfee provides regular insight on global hacking scandals and internet surveillance, and has become a hugely controversial figure following his time in Belize, where he claims to have exposed corruption at the highest level before fleeing the country amid accusations of murder (the Belize government is currently not pursuing any accusations against him).
In September 2015, John McAfee was nominated for Technology and Digital Commentator of the Year at the annual Comment Awards for his work for IBTimes UK. The winners will be announced at a ceremony on 24 November.
© Copyright IBTimes 2025. All rights reserved.




















