Is Samsung Pay vulnerable to hackers?
Samsung has played down the reports, claiming a hack is 'extremely unlikely'.
With contactless payments now commonplace, it comes as no surprise that hackers are trying to exploit these systems for financial gain.
One white-hat hacker, Salvador Mendoza, has revealed a successful technique that can be used to exploit Samsung Pay by intercepting digital tokens – generated to represent credit card details – to make fraudulent purchases.
The findings, which were presented at the recent Black Hat hacker conference in Las Vegas, have been played down by Samsung which said it was aware of the researcher's claim but assured users such a hack is "extremely unlikely" to occur in real-life.
In his presentation, Mendoza demonstrated how he could intercept digital tokens using a 'skimming attack'. The tokens, which are single-use and expire after 24 hours, are transferred from a user's smartphone to a payment terminal via a wireless connection.
The researcher said an attacker can extract tokens generated by the Samsung Pay application using a small device called 'TokenGet', which is specifically programmed to intercept the codes in real-time and transfer them directly to the hacker's computer.
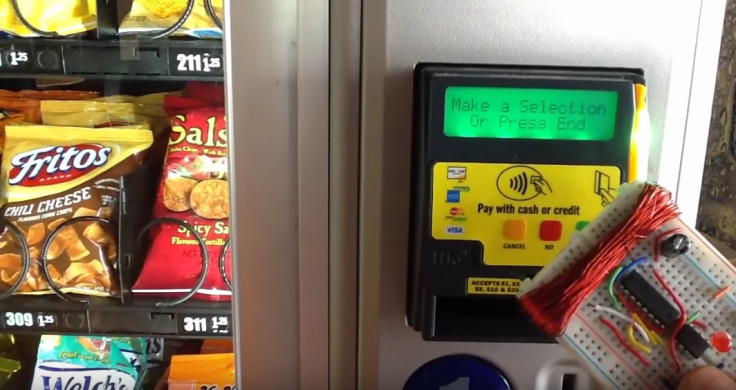
Once the hacker has stolen the digital token, Mendoza demonstrated how a credit card strip emulator called 'MagSpoof' can then be used to make fraudulent purchases. To show his findings to a wider audience, the researcher also uploaded his technique to YouTube.
The footage shows the exploit in action, eventually being used to purchase a product from a vending machine using intercepted tokens. Mendoza also uploaded his code to GitHub.
Responding to the findings, Samsung said: "We are aware of a recent and inaccurate report regarding the security of Samsung Pay. We would like to clarify that Samsung Pay is built with highly secure technology and is the most widely accepted mobile payment solution available today."
However, in an extended FAQ page released on its security blog, the smartphone firm appeared to admit the exploit was possible. The main difficulty, Samsung claimed, was that a hacker has to be close to the target in order to intercept their tokens.
It elaborated: "In order for this 'token skimming' to work, multiple difficult conditions must be met. First the user must permit the token and cryptogram generation with his or her own authentication method. This pair of token and cryptogram must be transmitted to the Point of Sale for each transaction and cannot be used for multiple transactions. Then the fraudster needs to capture the signal on a device that is within very close proximity to the Samsung phone."
To counter the claim, Mendoza then uploaded another video to YouTube in an attempt to prove Samsung wrong.
In the description, he wrote: "According to the last official statement from Samsung denying any issue with its tokens, I made this video without cutting or editing nothing from it, making a transaction using MagSpoof. According to Samsung's statement this transaction had to be declined. But it went through. Why?"
© Copyright IBTimes 2025. All rights reserved.






















