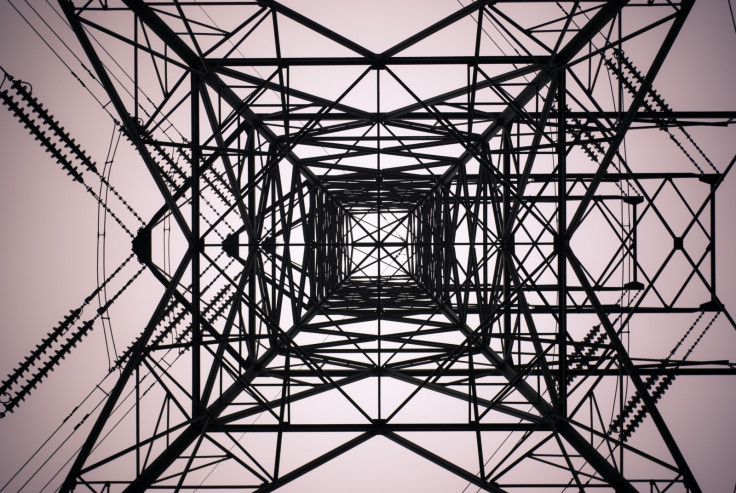
Western energy sector at risk of total sabotage by new 'Dragonfly' hacking campaign
Resurgence in energy sector attacks linked to 'Dragonfly' cyber espionage unit.
A highly experienced and possibly state-sponsored hacking group codenamed 'Dragonfly' may be gearing up for fresh sabotage cyberattacks on the energy sector in Europe and North America, according to research released this week (6 September) by Symantec.
Dragonfly has been active since 2011, but went dark for a short period of time after being exposed by security researchers in 2014. Now, a campaign that has been ramping up gently since 2015 may be entering a new, and highly disruptive, phase of operations.
"This is clearly an accomplished attack group," Symantec warned in its latest threat report on the unit.
Like prior campaigns between 2011 and 2014, the new Dragonfly campaign relies on a number of specific infection techniques including malicious emails, booby-trapped websites and Trojans. It is uses custom malware that is not available on the black market.
The initial phase, the security firm said, appears to have been exploratory "where the attackers were simply trying to gain access to the networks of targeted organisations" to plan future cyber-assaults.
Often, Symantec said, sabotage attacks are "preceded by an intelligence-gathering phase where attackers collect information about target networks and systems".
This was the case with the Stuxnet and Shamoon attacks, both linked to nation states.
While it did not release names of the targets, Symantec noted that exploitation of an energy firm could result in power outages, shutdown of electrical grids or disruption to utilities. The group "now potentially has the ability to sabotage", researchers revealed.
It's important to note, however, that the nightmare scenario of complete takeover of critical energy systems remains speculation and theory at this time.
The majority of new activity has been spotted in the US, Turkey and Switzerland. In 2016 and 2017, the group conducted a malicious email campaign that contained "very specific content related to the energy sector" and aimed to hijack sensitive network credentials.
This year, Symantec observed the group using a toolkit known as "Phishery" which has been publicly available since last year and used to to infect unwitting targets. In one instance, a victim was re-directed to a malware-ridden website and their computer was hacked 11 days later.
Dragonfly is widely considered to be an advanced persistent threat (APT) group and is also known to researchers under the names Energetic Bear and Crouching Yeti. In 2014, Symantec said that it "bears the hallmarks of a state-sponsored operation" that engages in espionage.
As such, the identities of the hackers remain a mystery. Experts say that they use a variety of tactics to stay hidden – often using publicly available malware or toolkits and staying away from "zero-days", which are exploits for software flaws known only to the cybercriminal.
Some code was in Russian, but some was also written in French, researchers said. This likely means that one code-set, Symantec claimed, was a "false flag". Nevertheless, experts believe that the group likely has the ability to gain control of energy systems and critical infrastructure.

Across the world, there has been a spike in energy sector attacks in the past two years. The most notable incident occurred against a power grid in Ukraine back in 2015 which left hundreds of thousands of people without electricity for hours. Russia was the main suspect.
Symantec believes that similar attacks may soon become more common. Researchers stated that Dragonfly is now "capable of compromising numerous organisations, stealing information, and gaining access to key systems". Its ultimate aim, however, remains ambiguous.
"What it plans to do with all this intelligence has yet to become clear, but its capabilities do extend to [disrupting] targeted organisations should it choose to do so," Symantec said.
© Copyright IBTimes 2025. All rights reserved.


























