Will UK Government's Cyber Streetwise Campaign Make a Difference? We Ask the Experts
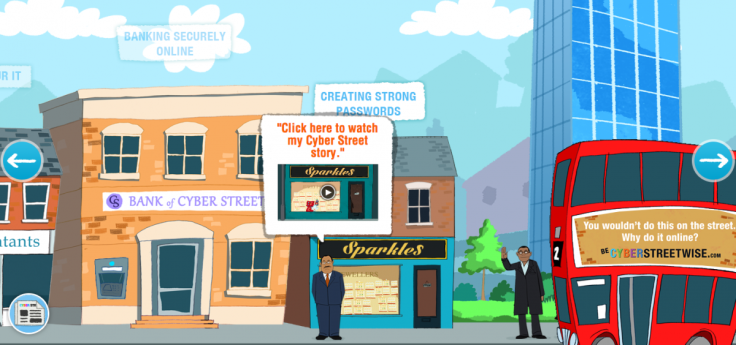
Offering a range of interactive resources and advice on everything from choosing a strong password to banking securely online, Cyber Streetwise is an initiative from the UK government which aims to raise the bar in relation to how securely we use the internet.
While resourceful cyber-criminals and pernicious malware may grab most of the headlines, the biggest problem facing consumers and businesses in relation to online security remains the use of weak passwords and failing to update software.
In short, the weakest links in the cyber security chain are you and me.
The UK government is looking to address this issue with the Cyber Streetwise website, which offers basic advice for consumers and individuals on subjects such as recognising a phishing email; how to keep your devices up to date; and what information you should, and should not, put on social media pages.
This is all part of the UK government's four-year Cyber Security Strategy which was launched in 2011.
But is Cyber Streetwise going to have any real impact? We decided to ask the experts:
Sean Sullivan, security researcher at F-Secure
Sullivan says he is "on the fence" regarding Cyber Streetwise. Some have suggested that the only problem holding back better cyber-security standards was a lack of good information, but Sullivan says: "I don't think that's the problem."
I suspect that a little knowledge is probably a dangerous thing — some user education can create a dangerous false sense of security.
Referencing a financial research paper which suggested that people who knew something about mortgages would actually take bigger financial risks and so demonstrated a false sense of financial security, Sullivan says: "I suspect that a little knowledge is probably a dangerous thing — some user education can create a dangerous false sense of security."
However, Sullivan does praise the UK government for at least doing something: "I like that [UK] government is trying to share information. I just get nervous that it could do more harm than good. It's a difficult issue."
Ron Gula, CEO of Tenable Network Security
Gula is more effusive in his praise of Cyber Streetwise:
"The right education and training can significantly reduce the frequency of security breaches. It can help staff to identify suspicious emails, know how some of the attacks work and teach staff what to do if they become compromised.
"While limiting and monitoring employee access to the internet can help reduce the risk of social engineering attacks, it is only by teaching people about the threats online, that they may be inclined to accept a more stringent internet usage policy."
Scott Greaux, VP of Product Management and Services at PhishMe
Greaux says that while this is the right move by the government, ultimately it will be futile:
"Focusing on consumer protection is the appropriate way for governments to participate in cyber awareness efforts. History tells us that these campaigns are not effective in changing behaviour or improving the overall security posture of private citizens but they can serve as a reliable resource for those who are interested and curious about how to better protect themselves."
Sarb Sembhi, member of ISACA Security Advisory Group
Sembhi pulls no punches when describing the new site, calling it too simplistic and condescending:
In my opinion, the website is too simplistic to look at, too complex to get to what you want and at the same time too condescending to the user.
"In my opinion, the website is too simplistic to look at, too complex to get to what you want and at the same time too condescending to the user.
"It just seems like the typical 'Let's be cool and make it like a street, since we want users to be streetwise.' I don't think the information is necessarily any better than you can find anywhere else. If they had put all the information as a list instead of having to navigate around a street to see what is available, that would have been simpler."
Matt Palmer, member of ISACA Security Advisory Group
Palmer, also a ISACA member, is more positive about the site, but he believes this is not the complete solution:
"This is an extremely useful resource for small business managers, who are often pressured for time and do not have access to internal expertise. Implementing all the areas highlighted will provide some basic protection against low-level threats and significantly reduce risk.
"However, it should be clearer that the good practices listed are a starting point for effective small business security, not a complete solution."
© Copyright IBTimes 2025. All rights reserved.




















