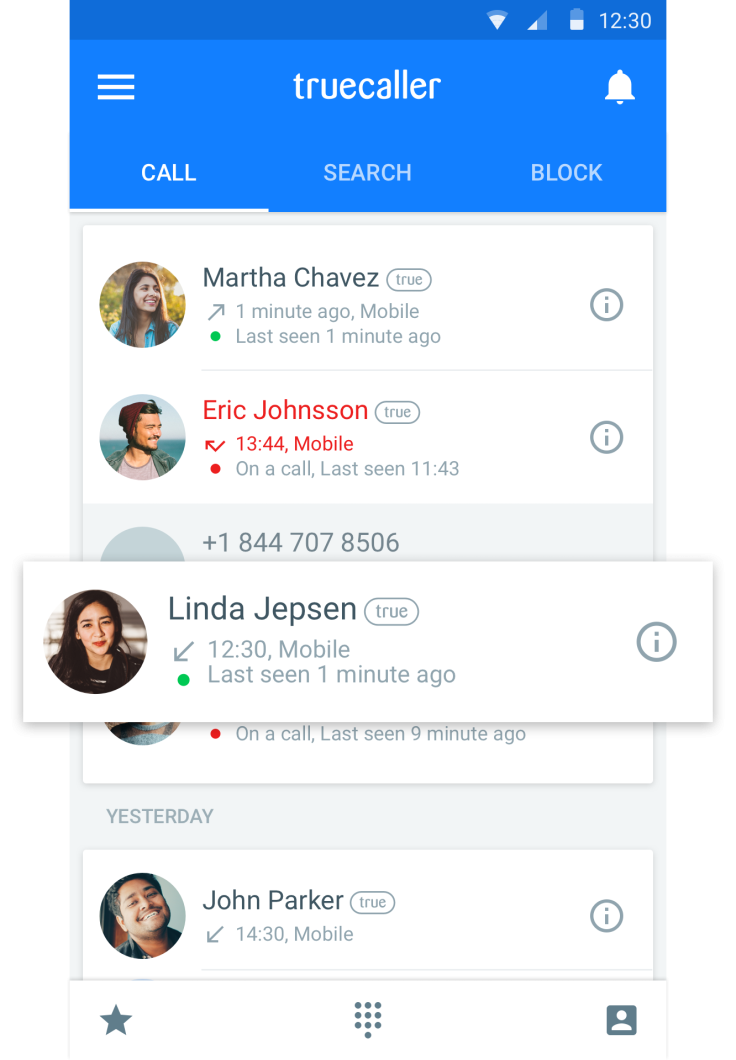
Caller ID apps publicly exposing names and numbers from your phone's address book
Popular mobile apps uploading users' address books to provide caller ID and reverse look-up functions.

Popular smartphone apps providing call blocking and caller ID functions are systematically uploading users' address books to publicly-accessible databases, where the name, phone number and even linked social media profiles can be seen by anyone.
The phone numbers and identities of some three billion smartphone users are reported to have been exposed by caller ID & blocking apps including Truecaller, Sync.ME and Cheetah Mobile's CM Security, reports the Hong Kong Free Press. All three apps can be downloaded for free from Google Play and the Apple App Store and between them boast several million users – Truecaller alone touts 100 million.
Truecaller, Sync.ME and CM Security all have a "reverse look-up" feature that allows users to identify callers even when they are not in their device's address book. In order to power this function, the apps need to collect users' contact lists and upload them into a database, which then allows an unknown number to be matched with a name.
This means even users who are not registered with the apps but reside in the address book of someone who does have had their contact details exposed by the services, despite the fact they have not given consent. The Hong Kong Free Press was able to look up several prominent government officials and businesspeople using the search function in Truecaller and CM Security, including the phone numbers belonging to Hong Kong Chief Executive Leung Chun-ying and former Secretary for Security Ambrose Lee Siu-kwong.
It also noted that the names in the database were not in a fixed format and were occasionally listed under nicknames, suggesting they came from users' address books, meanwhile Sync.ME also contained information on users' social media profiles.
Truecaller, Sync.ME and CM Security all state in their privacy policy that the apps may collect contact information stored in users' devices in order to provide their caller ID and blocking services. They also state that users' address books will be merged with those of other registered app users in order to provide a database of searchable contacts.
Lack of consent
Truecaller told IBTimes UK that users cannot get a number from the service unless the owner gives permission, with "non-public" numbers shown as "private" by default. Meanwhile, Sync.ME's privacy policy states that users must "have all necessary permissions to share your contacts' information, and that you have no knowledge of any objection, on the behalf of any of your respected contacts, top include their names and phone numbers in the phonebook directory, which is available for other registered users."
Both Truecaller and Sync.ME allow users to opt-out of sharing contact information, although CM Security doesn't appear to offer such a clause.
A Cheetah Mobile spokesperson told IBTimes UK that it had since disabled the reverse look-up function in CM Security "to prevent any other malicious action intended to expose users' private information."
"CM Security, developed by Cheetah Mobile, is a mobile security app featuring an antivirus engine and call identification for Android," said the spokesperson. "Its 'Caller ID' function, along with look-up features, helps users to identify suspicious calls and avoid unwanted calls, harassment or phone scams. This is one of the most beloved features of CM Security.
"The Caller ID database is contributed to by our global partners, from users' feedback and directories uploaded with users' approval. The feature was designed for users to proactively report phone fraud and phone scams, and at the same time avoid unwanted calls. While our intention is to maximise call identification function, it's unfortunate that this was misused.
"The privacy concerns will only occur with the deliberate reverse search for certain phone numbers which are already known by the people conducting the search...In addition, all user data in CM Security and WhatsCall is stored in AWS, and encrypted to ensure the best data security and privacy protection."
'Pillaging' customer details
Javvad Malik, security advocate at AlienVault, told IBTimes UK that while it was common for mobile apps to gather lots of personal information, the scale at which Truecaller, Sync.ME and CM Security appeared to collect it was concerning.
"Given the number of mobile apps that gather or leak a lot of personal information, it is unfortunately not unusual," he said. "Putting that aside, pillaging all customer contact details certainly isn't what I would term business as usual."
"From a legal perspective, putting a clause somewhere inside the terms & conditions (which hardly anyone reads) one could argue that the company has been transparent. However, the reality is that companies know that users tend to not read the legal verbiage when downloading a new app. So, from a practical point of view – no, these companies have not done enough. Had customers been fully informed of the implications, it is likely fewer would have signed up."
Sync.ME has yet to reply to a request for comment from IBTimes UK.
© Copyright IBTimes 2025. All rights reserved.





















