Car washes can be hacked to physically attack you and your vehicle
Doors can be locked and vehicles attacked with water and mechanical arm.
In scenes resembling a new Final Destination film, cybersecurity researchers have discovered a way of hacking into an internet-connected car wash and trapping customers inside, before attacking them with its mechanical arm, doors and water jets.
The hackers were able to log into the car wash remotely, enter its "easily guessable" password, then take control of its doors and a mechanical arm used to spray water and wax at vehicles. Warning systems to stop the machine inflicting damage on a car can be shut down, letting hackers hit vehicles with the arm and doors, or lock the doors and spray water continuously to prevent customers from easily escaping.
To be presented at the Defcon security conference in Las Vegas this week, the exploit was discovered by a team led by Billy Rios, founder of Whitescope Security.
"We believe this to be the first exploit of a connected device that causes the device to physically attack someone," Rios told Motherboard.
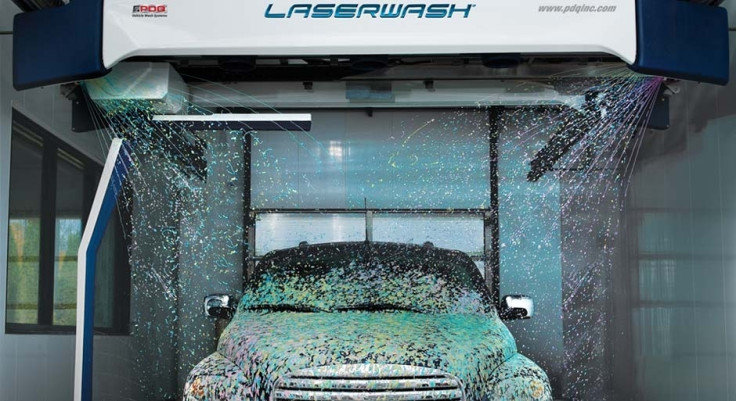
The car wash was a PDQ LaserWash, which runs Windows CE and is a fully-automated system controlled by customers via a touch screen. An internet connection is used for technicians to configure its settings remotely.
This connection is the wash's weak spot. Rios says, despite not all PDQ systems being online, he discovered over 150 washes ready to be hacked via Shodan, a search engine which shows internet-of-things devices like printers and webcams. Although the password was apparently easy to guess, Rios said a vulnerability meant this could also be bypassed instead.
A script was then written which took control of the car wash and made it do whatever the researchers asked of it. Infrared sensors used to prevent the car wash from damaging vehicles with its doors and moving arm can be disabled, allowing hackers to inflict as much damage as they like to the washer, the car inside and potentially the driver and passengers should they try to escape.
Rios told Motherboard: "If you're relying purely on software safety, it's not going to work if there's an exploit in play. The only thing that's going to work [here] is hardware safety mechanisms."
PDQ said it is "aware" of the hack, adding: "All systems - especially internet-connected ones - must be configured with security in mind. This includes ensuring that the systems are behind a network firewall, and ensuring that all default passwords have been changed. Our technical support team is standing ready to discuss these issues with any of our customers."
© Copyright IBTimes 2025. All rights reserved.






















