Hackers could steal your data just by using the LED lights on your computer
Air-gapped computers are typically hard to hack, but one team in Israel has found a way.
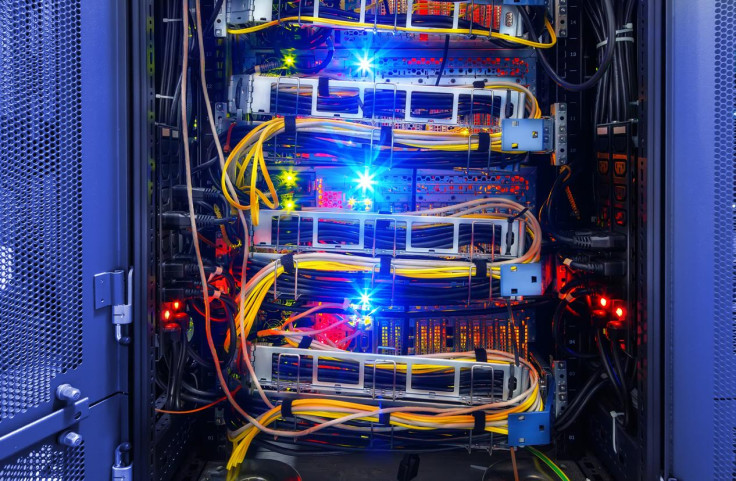
Hackers may be able to covertly steal sensitive data, including passwords, from isolated computer systems by using the blinking LED lights built into PCs, laptops and servers, research suggests. The method takes advantage of the flickers that represent the activity of hard disk drives (HDDs).
The claim comes from researchers at Ben-Gurion University of the Negev, Israel, who have released analysis showing how a hacked air-gapped computer can leak critical information via these LED lights. On 22 February, the team released a YouTube video showing the 'hack' in action.
How hacking via LED lights works
"Sensitive information can be encoded and leaked over the LED signals, which can then be received remotely by different kinds of cameras and light sensors," the team, led by Dr Mordechai Guri, head of R&D at the Cyber Security Research Centre, said in its paper.
"We show how the malware can indirectly control the status of the LED, turning it on and off for a specified amount of time, by invoking hard drive's 'read' and 'write' operations," the paper continued. "Our method is unique in two respects: it is covert and fast."
What hackers can steal
The paper explained what a theoretical attack would look like once infection had taken place. The team wrote: "The malware gathers sensitive information from the user's computer, e.g., keystrokes, password, encryption keys, and documents.
"Eventually it starts transmitting the binary data through the blinking HDD LED using a selected encoding scheme. A hidden video camera films the activity in the room, including the LED signals. The attacker can then decode the signals and reconstruct the modulated data."
It added: "We examined the physical characteristics of HDD LEDs [...] and tested remote cameras, extreme cameras, security cameras, smartphone cameras, drone cameras, and optical sensors. Our results show that it is feasible to use this optical channel to efficiently leak [data]."
Should we be worried?
As this technique is aimed specifically at targeting air-gapped systems, which means they are isolated both logically and physically from public networks and not connected to the internet, it remains difficult. Such systems typically contain an organisation's most confidential information.
The hackers would have to design tailored malware to control and decode the blinking LED transmissions, never mind installing it on a system that is typically well-guarded. Lastly, they would need a method of reading the blinks be it drone, CCTV camera or wearable bodycam.
"But despite the high degree of isolation, even air-gapped network are not immune to breaches," the team said in its paper. An attacker can use social engineering tactics, supply chain attacks or even rely on computer hardware with pre-installed malware to infect the targeted system.
Dr Guri, in a statement on the same day the paper was published, said: "Our method compared to other LED exfiltration is unique." Stressing its covert capability, he added: "The hard drive LED flickers frequently, and therefore the user won't be suspicious about changes in its activity."
There are a number of countermeasures that firms using air-gapped systems can take to put an end to this attack vector, the researchers said. These include tightly restricting staff access to such computers or banning all forms of video cameras near the computer. It also noted one, slightly less sophisticated idea: covering the LED light with black tape.
You can read the full paper here.
© Copyright IBTimes 2025. All rights reserved.




















