Hackers targeted Clinton and Trump websites using Mirai botnet before Election Day
The same Mirai malware was used to take down a part of the internet in the US and UK in October.
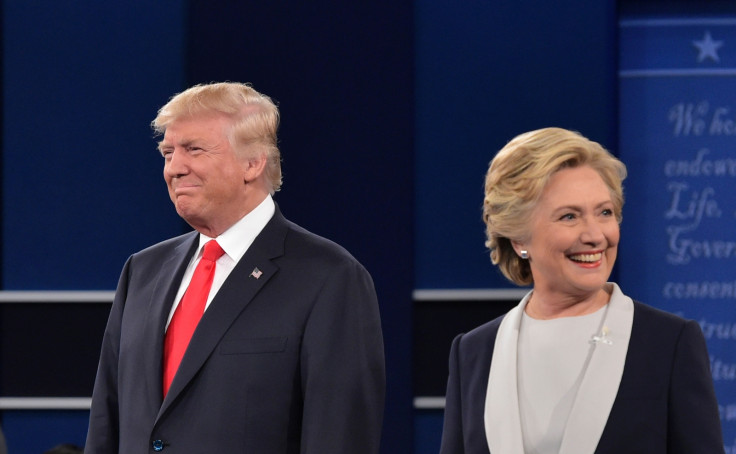
Hackers tried to cripple the campaign websites of US presidential candidates Hillary Clinton and Donald Trump this week employing the same Mirai malware used to take down a part of the internet in the US and Europe in October. According to security firm Flashpoint, four 30-second HTTP Layer 7 attacks were detected between 6-7 November. However, they note that neither site experienced any outages because the Mirai botnet is getting weaker.
"Flashpoint assesses with moderate confidence that the Mirai botnet has been fractured into smaller, competing botnets due to the release of its source code, which has led to the proliferation of actors exploiting the botnet's devices," the firm said. Researchers said they do not believe that the attacks were the work of nation-state actors, but were likely the work of "unsophisticated actors" using the Mirai IoT botnet to target the candidates' sites.
Earlier in October, hackers released the source code for the Mirai malware which experts warned would set off multiple cyberattacks from new botnets powered by compromised web-connected devices. Later the same month, hackers launched waves of distributed denial of service (DDoS) attacks by hacking IoT devices to create a huge botnet of compromised connected devices and target DNS provider Dyn with a deluge of fake traffic.
"This release has caused many hackers to compete with one another for control of IoT devices that remain susceptible to Mirai malware," the researchers said. "In order for these hackers to launch large-scale DDoS attacks successfully - outperform competitors who are vying to control the same type of devices.
"Though not impossible, overcoming this competition is a considerable challenge and so far, the IoT botnet landscape appears to be saturated with too many would-be controllers and not enough new vulnerable devices."
At least one hacker going by the name Jono Gaukster has claimed responsibility for the first set of cyberattacks against Trump's website half an hour after it occurred. However, Flashpoint could not independently verify the claim.
@realDonaldTrump Hey Trump do you mind DDOS attack on you? #JustWandering
— Jono Gaukster (@omegadragon97) November 6, 2016
"So far, these DDoS attacks have been limited to the nominees' website infrastructure and have not targeted - nor affected - any infrastructure associated with the actual electoral process," the researchers noted. "This attack, in addition to other more powerful, higher-profile attacks associated with the Mirai botnet, all align closely with tactics, techniques, and procedures commonly executed by hackers operating from underground forums."
There have been serious widespread concerns about possible cyberattacks surrounding Election Day providing a "fertile ground" for cybercriminals since most tend to be "primarily motivated by the desire for attention, credibility, or 'trolling' via disruption".
Flashpoint previously found that the massive Mirai DDoS attack from October was more likely the work of "script kiddies" rather than organised cybercriminals, hacktivists, state actors or terrorist groups.
© Copyright IBTimes 2025. All rights reserved.



















