How to check if your email address has been hacked by cybercriminals
Find out if your email address is insecure and how to create a stronger password.

With the sheer amount of cyberattacks and data breaches these days, it's highly likely at least some of your personal information, including email addresses, have been compromised at some point. If you want to be sure, there's one handy way you can check right now.
Dubbed Have I Been Pwned, it's a free online service founded by an Australian computer expert and data breach connoisseur called Troy Hunt and continues to be the quickest and easiest method to test how clean your online accounts really are. There have been others in the past, such as LeakedSource, however Hunt's is one of the few to stay on the right side of the law.
How to check if you've been hacked
It's a simple process: visit haveibeenpwned.com, input your email address and click enter. If the screen turns red, your account is deemed to have been pwned (internet lingo for owned) and is stored within one of the two million-plus credentials on the website.
Hunt has compiled emails from over 190 breached websites, a figure that appears to be rising with each passing week. Some of the biggest names are huge technology companies including, Yahoo, LinkedIn and Dropbox alongside a slew of web forums.
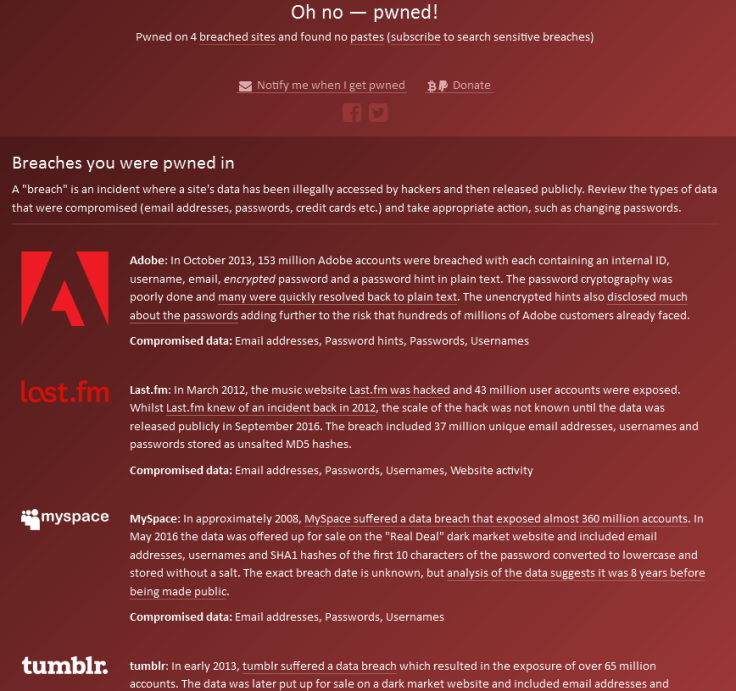
In one test conducted by IBTimes UK, a relatively new email address was inserted into the search bar. "Good news – no pwnage found!" was the result. However, in another test on a rather ancient one, the message read: "Oh no – pwned!"
It turned out the old account was found in four separate security breaches: Adobe, Lastfm, MySpace and Tumblr. This is helpful because it helps you to tell what emails – and therefore passwords – are likely to be in the hands of hackers or cybercriminals.
"I created 'Have I Been Pwned' as a free resource for anyone to quickly assess if they may have been put at risk due to an online account of theirs having been compromised or 'pwned' in a data breach," Hunt wrote on the website.
"I wanted to keep it dead simple to use and entirely free."
He continued: "This site serves two primary purposes for me: firstly, it obviously provides a service to the public. Data breaches are rampant and many people don't appreciate the scale or frequency with which they occur.
"Secondly, the site provided me with an excellent use case for putting a number of technologies through their paces and keeping my hands-on skills somewhat current."
What to do if you email has been hacked
If you find your email address on the website, the advice is to change your credentials immediately or close the account altogether. If the service has a two-step authentication option, use it to add a secondary layer of protection and security.
Additionally, the usual tips apply: keep passwords long, unique, with a mixture of characters, numbers and symbols. Personal credentials should never be used on other online services – be it social media or banking – and if in doubt consider using a password manager.
Its common knowledge that password use remains poor, despite the uptick in cybersecurity threats in the wild. In a blog post published in January 2017, Darren Guccione, co-founder of Keeper Security, revealed some people still use credentials as weak as '123456' or 'p@ssword'.
His firm analysed 10 million passwords from data breaches that happened in 2016 and found that four in 10 breached accounts were six characters or shorter. "Looking at the list of [the year's] most common passwords, we couldn't stop shaking our heads," he wrote.
How to create a more secure password
According to the recently-opened National Cyber Security Centre (NCSC), a fork of the UK intelligence agency GCHQ, password strength remains a vital factor of staying safe online.
"Our research shows that the best way to make a password memorable and strong is to use three random words," a spokesperson from the NCSC told UK advice website Action Fraud.
"Thinking random is the best way to keep yourself secure online. Your most important accounts are your email, social media and online banking accounts, so it's important to use strong, separate passwords for each of these."
© Copyright IBTimes 2025. All rights reserved.




















