New York airport leaks over 750GB-worth of emails, passwords and government files
Huge database leak a 'complete compromise' of airport network integrity, expert says

For months, the Stewart International Airport in New York was reportedly exposing sensitive internal data onto the internet without password protection. The data – over 750GB in total – has been described as a "complete compromise" of its network integrity.
According to MacKeeper security researcher Chris Vickery, the massive trove of sensitive data was wide-open to theft or compromise until as recent as this week (21 February) and had been publicly available since at least March last year.
In a blog post, Vickery said documents suggest Stewart International's digital security is managed by a private firm called 'AVPorts'. A firm which, at least according to its website, offers "unrivalled integration of airport management capabilities, experience and expertise."
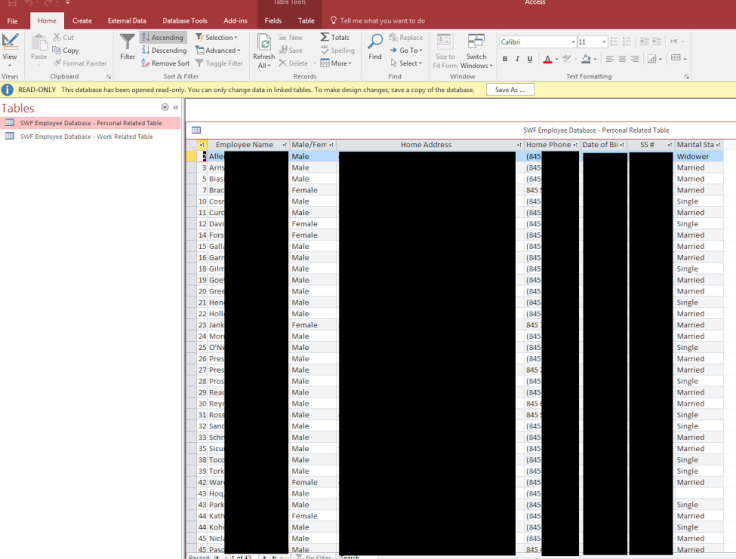
The leaked data includes 107GB-worth of personal email correspondence from within the airport alongside letters from the Transportation Security Administration (TSA), a federal agency linked to the US Department of Homeland Security (DHS).
Vickery said it also included employee social security numbers (SSNs), payroll records and even network passwords. Many of the documents in the leak included marks such as 'For Official Use Only' and 'Unauthorised release may result in civil penalty.'
Worryingly, the private firm contracted to manage the security of the airport by its owners, the Port Authority of New York and New Jersey, was reportedly a one-man operation. Vickery said the IT technician is only on-site "two or three times" per month.
He wrote: "For-profit companies have every incentive to, all too often, prioritise revenue over best practices. This is emphasised by the AvPorts incident response performance.
"In an industry at the level of airport management, every employee needs to have at least cursory data breach readiness training. The first person I spoke with at AvPorts was very nice to me, but at one point asked me if this 'could wait until tomorrow'."
The breach has been blamed on a mixture of two-factors. One, the airport experimenting with a backup software called 'Shadow Protect'. And two, the use of a problematic secondary backup device called a Buffalo Terastation, which has been at the centre of past breaches.
According to ZDNet – which obtained and exclusively reported on the leak – one file contained a list of passwords for airport systems which if abused would have allowed "unfettered access" to the airport's network. This was verified by two separate researchers, it reported.
The Port Authority of New York and New Jersey told ZDNet: "There is no indication of a direct breach, or of malware installed on [our] network.
"We are being provided with a copy of the back-up file, system logs, network diagrams and their firewall configuration, to determine whether there are any ongoing risks or vulnerabilities to the agency's data. Until we examine the backup file, we can't be sure of the contents, but we don't believe it contained customer passenger data."
© Copyright IBTimes 2025. All rights reserved.