iOS 7.1 Beta 4 May Patch Key Exploits in Evasi0n7, Says iH8sn0w
MuscleNerd declines to say if exploits are closed in iOS 7.1 beta 4 as it may help Apple to fix it
With Apple's recent release of iOS 7.1 beta 4 to developers, the jailbreak community is wary of losing key exploits in evasi0n7 and hence anxious to find out if the update actually patches up vulnerabilities in the untethered jailbreak.
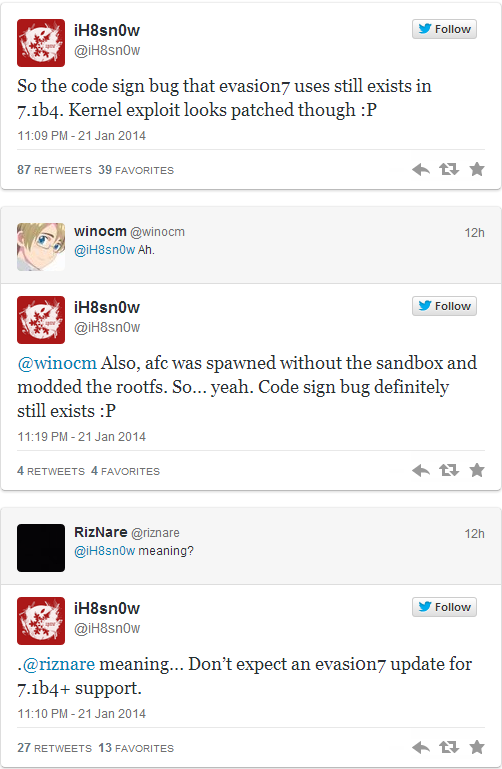
As iPhone Hacks notes, there is some bad news for potential iOS 7 jailbreakers as the developer of p0sixpwn, iH8sn0w, has hinted that a key Kernel exploit appears to be patched in the latest beta iteration of iOS 7.1.
Furthermore, iH8sn0w clarifies that the code sign bug is still working in iOS 7.1 beta 4 and asks jailbreakers not to expect an evasi0n7 update with 7.1b4+ support.
Here is what iH8sn0w tweeted to his followers in response to their query about Apple's beta 4 release for iOS 7.1:
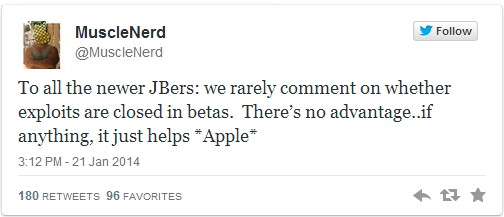
On the contrary, evad3rs have not yet commented on this issue or confirmed the existence of a patch for key kernel exploits used in evasi0n7 untethered jailbreak. The popular iOS hacker and Jailbreak developer, MuscleNerd, has also declined to comment if the exploits are closed in betas.
MuscleNerd guards against complacency and tweets to his followers that there is no real advantage in revealing details about patched exploits in the new beta 4 update for iOS 7.1, as it will only help Apple to patch up all known exploits used in evasi0n7 with its upcoming release.
Here is what MuscleNerd tweeted to his followers:
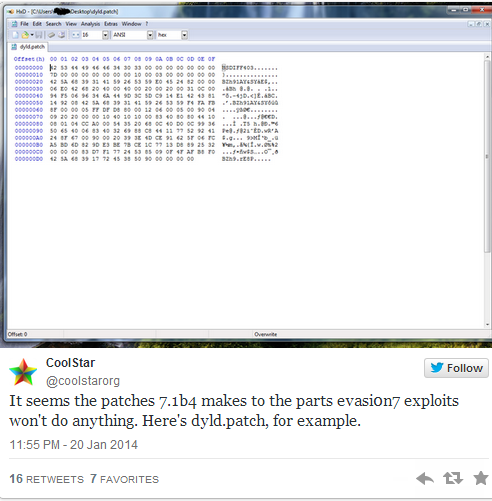
Another veteran jailbreak developer, CoolStar, had this to tweet while explaining the effects of iOS 7.1 beta 4 on evasi0n7 jailbreak:
With rumours pointing to an Apple release of six beta iterations for iOS 7.1, it is likely to fix the code signing bug during this period for an edge against jailbreakers and evad3rs. As iDownloadBlog reports, if Apple turns out successful in doing so, then the existing evasi0n7 jailbreak needs to be reworked to use different exploits, or completely scrapped and rebuilt.
It is still unclear if Apple will kill the evasi0n7 jailbreak before or after its final iOS 7.1 update, while uncertainty surrounds the release timeframe for the next evasi0n7 jailbreak.
© Copyright IBTimes 2025. All rights reserved.






















