Jamie Oliver website still serving malware to visitors a month after breach discovery
Celebrity chef Jamie Oliver's official website is still serving up malware to users a month after it was discovered that the website had been compromised by hackers. Security firm Malwarebytes discovered on 19 February, 2015, that jamieoliver.com had been compromised with code injected into the JavaScript on the homepage that embedded a malicious website directly into the website.
The malicious website contained the Fiesta exploit kit which then tried to attack users' computers if they were not running the latest patched versions of Adobe's Flash, Microsoft's Silverlight, and Java.
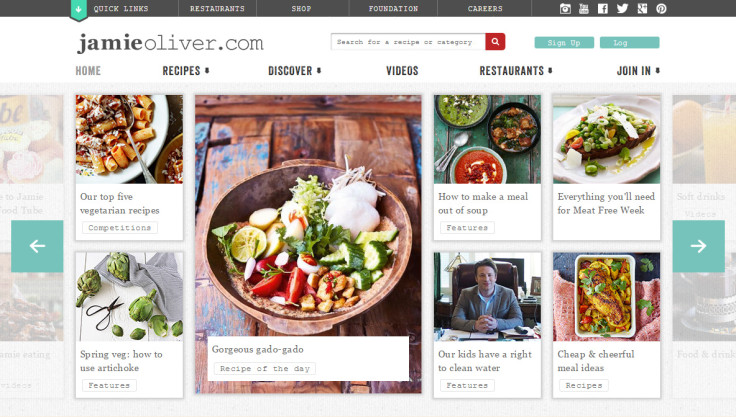
Jamie Oliver's website receives an average of 10 million visitors a month and provides recipes and information about his various books, TV shows, restaurants and projects. The website is believed to have been hacked in December 2014 and had been serving up malware for two months until it was spotted.
Jamie Oliver's management team announced on 19 February, 2015, that they had solved the problem and that the site was now safe to use, but Malwarebytes has now discovered that more malicious code is embedded in the website's homepage that also redirects back to the Fiesta exploit kit.
"This is basically the same structure as we observed in the previous hack, which leads us to believe this is the same infection that was not completely removed or perhaps that a vulnerability with the server software or Content Management System (CMS) still exists. It is indeed quite common for a hacked server to retain malicious shells or backdoors that keep on reinfecting the site," Malwarebytes' senior security researcher Jérôme Segura writes in a blog post.
IBTimes UK has contacted Jamie Oliver's management team for comment on the malware situation.
For now, users are advised to boost their online security by making sure that all their software is up-to-date, including their firewall and anti-virus software. Concerned users can also install free anti-exploit software, which prevents hackers from exploiting vulnerabilities in web browsers, browser add-on plugins and JavaScripts.
On the other hand, website owners would be advised to scan their websites in order to see if there are any vulnerabilities, since if it can happen to a well-known celebrity website, it can happen to anyone.
There are several free online malware and security vulnerability scanners, including Penguin Scan, Sucuri SiteCheck, Quttera, and VirusTotal.
© Copyright IBTimes 2025. All rights reserved.




















