New Java Vulnerability Being Exploited by Blackhole-based Attacks
A new vulnerability discovered in Java 7 has been commoditised and websites exploiting it are already being discovered.
Oracle's Java Runtime Environment (JRE) is known among security experts as a pretty insecure platform and earlier this week a new, highly exploitable vulnerability was discovered which targeted users of Java 7.
Security expert with F-Secure, Sean Sullivan, dubbed JRE as a Perpetual Vulnerability Machine when he reported on its discovery earlier this week.
FireEye first reported the flaw being used in a targeted attack originating from a Chinese web server. The web page hosting the exploit is timestamped 22 August, 2012.
While it was initially reported that the Chrome browser was immune to attack, that has now been shown to be untrue and the Metasploit project has released proof-of-concept code that exploits the flaw on all browsers and operating systems (Windows, OS X, Linux).
Within days of the vulnerability - known as CVE-2012-4681 - being discovered, cyber criminals commoditised it and have now rolled out a new version of the Blackhole exploit kit which takes advantage of the vulnerability.
"The first victim regions to be hit with the Blackhole stuff were the US, the Russian Federation, Belarus, Germany, the Ukraine and Moldova," Kaspersky Lab expert Kurt Baumgartner said on the Securelist blog.
Blackhole is one of the most popular of the commercial exploit kits and is used to automatically infect computers with malware when users visit malicious or compromised websites - in a method known in the industry as a drive-by download.
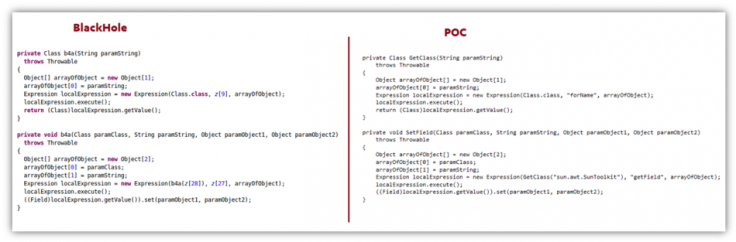
The developers of Blackhole sell it to cybercriminals and the kit contains a series of exploits which target known vulnerabilities in browser plug-ins such as Java, Adobe Reader and Flash Player.
Numerous security firms inlcuding Kaspersky Lab, F-Secure and Sophos has now confirmed that a version of Blackhole containing an exploit which takes advantage of the new vulnerability is in the wild and websites using it are already being reported.
Announcement
An announcement on this Russian underground malware website informs potential customers that the zero-day vulnerability has now been included in the latest version of Blackhole. A zero-day attack or threat is an attack that exploits a previously unknown vulnerability in a computer application.
Only people running Java 7 are affected by this latest vulnerability, meaning it may not affect that many computers, compared to older exploits, as a lot of people will not have upgraded.
"In relation to the other exploits included in the [Blackhole exploit kit] pack, victims are getting hit only a fair number of times with the [new vulnerability]. Internet Explorer users are being hit the most, followed by Firefox, Chrome, and Opera," Baumgartner said.
According to Rafal Los, a security strategist with HP Software, the fact this new vulnerability only affects those running the latest versions of Java 7 is a good thing.
"Perhaps one odd positive note for those, like me, who are still on Java 6 and haven't updated to Java 7, is that you're safe... so in an odd way not updating to the latest Java release actually saves your skin from an issue that has no resolution right now."
Oracle has not yet patched this vulnerability and its track record in issuing patches for Java has been, well patchy at best. Therefore to make sure you are protected against this latest vulnerability you'll need to switch off Java.
This requires you to check whether it is installed on your computer, and you can do this, and find out which version you have installed, by visiting this website. You will also need to disable the Java Web plugin installed on whatever browser you are using. This can be done from the settings menu.
However, Baumgartner believes it is up to Oracle to step up to the plate and begin delivering patches to these vulnerabilities:
"Oracle needs to step it up and deliver an OOB patch, which historically they have failed to do. Maybe this event will provide even more pressure to step up their security update delivery process. They have been snapping up some good security research talent and beginning to reach out, which is a start. A very late start."
© Copyright IBTimes 2025. All rights reserved.





















