Pwned Passwords: In 10 seconds, this new website could save you from being hacked
This new service contains 360 million pwned passwords that you should not be using.

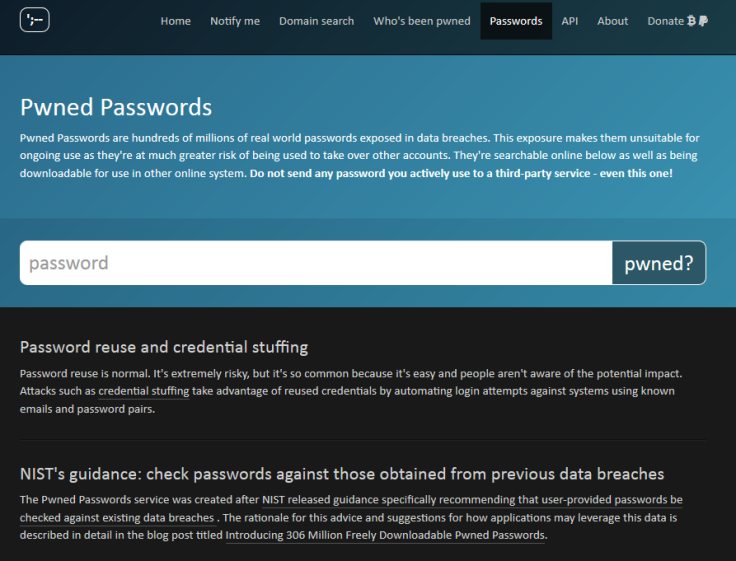
A security researcher has created an easy-to-use service which could save you the trouble of being hacked. When you are signing up to any new account you should be looking for a fresh, unique password – but what happens if it's already been hijacked? One new website lets you check.
In late July 2017, the National Institute of Standards and Technology (NIST) released guidance around the use of passwords, saying that organisations should consider blocking new accounts on their websites that use passwords previously discovered in major data breaches.
"I realised I was in a unique position to help do something about the problem they're trying to address due to the volume of data I've obtained," said Troy Hunt, the admin of HaveIBeenPwned, a service which lets you check if your email address has been compromised.
In a blog post, published 3 August 2017, Hunt explained how he amassed a total of 306 million pwned passwords from datasets stored on his repository and – with the help of Cloudflare – created the new capability.
Alongside the new service, which takes the form of a simple search bar, a full 11.9GB file is also available for firms to download and incorporate into their systems.
The passwords are not clear-text, instead provided as SHA1 hashes to keep individuals from being identified.
The website comes with a very clear caveat; users should not rely on the service for checking passwords associated with current accounts, be it social media or online banking. The service was instead designed to be a method of testing new credentials.
"It goes without saying but don't enter a password you currently use into any third-party service like this!" Hunt stressed in the blog post.
"I don't explicitly log them and I'm a trustworthy guy, but yeah, don't. The point of the web-based service is so that people who have been guilty of using sloppy passwords have a means of independent verification that it's not one they should no longer be using."
He continued: "Use this data to do good things. Take it as an opportunity to not just reduce the risk to the service you're involved in running, but also to help make people aware of the broader risks they face due to their password management practices.
"When someone gets a 'hit' on a pwned password, help them understand the broader risk profile and what this means to their personal security.
"One thing that's really hit home while running HIBP is that few things resonate with people like demonstrating that they've been pwned."
Hunt added: "I can do that with those who come to the site and enter their email address but by providing these 306 million pwned passwords, my hope is that with your help, I can distribute that 'lightbulb moment' out to a far greater breadth of people."
If a compromised password is entered, a bright red warning message is splashed across the screen. It reads: "Oh no — pwned! This password has previously appeared in a data breach and should never be used. If you've ever used it anywhere before, change it immediately!"
HaveIBeenPwned has become an industry-standard method of checking compromised credentials, and is currently storing a massive 3,914,073,118 pwned accounts from more than 200 websites. Significant past breaches include Exploit.In, Adobe, LinkedIn and Myspace.
"Password reuse is normal. It's extremely risky, but it's so common because it's easy and people aren't aware of the potential impact," the new website notes.
Hunt, in his blog post, expounded: "If there's one thing I've learned over the years of running this service, it's that nothing hits home like seeing your own data pwned."
© Copyright IBTimes 2025. All rights reserved.




















