This new dark web ransomware-as-a-service is customised so any script kiddie can launch attacks
The RaaS was found being sold for $175 by a Russian cybercriminal and allows users to remotely control and monitor attacks.
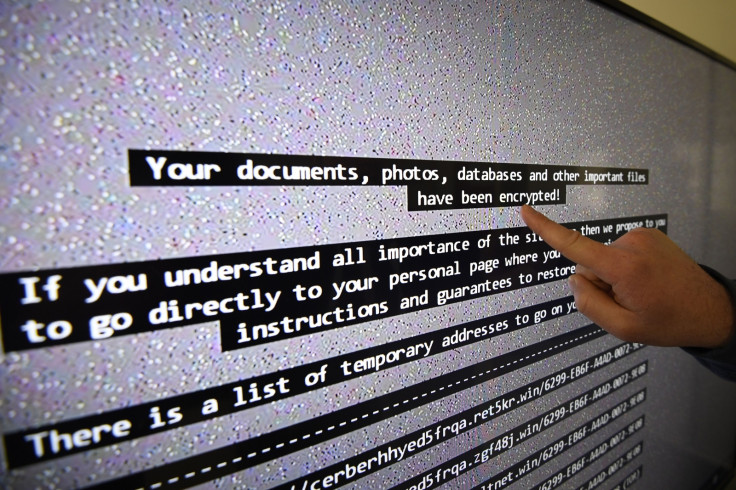
A new dark web ransomware-as-a-service (RaaS) has been uncovered by security researchers, which according to experts, is selling a new ransomware variant called "Karmen". The customised ransomware is being sold by a Russian-speaking cybercriminal "DevBitox," who goes by the username "Dereck1" on an unspecified "top-tier cyber criminal community", according to researchers who discovered Karmen.
Despite the fact that the Karmen ransomware variant was found for sale on the dark web in March 2017, first infections with Karmen were found to date back to December 2016, according to security researchers at Recorded Future. The ransomware, which like other variants, encrypts victims' data and demands a ransom to provide them with the decryption key, was found targeting victims in the US and Germany.
The ransomware has been specifically designed to be user-friendly to those with limited technical skills and/or knowledge and also employs advanced security evading techniques. For instance, Karmen will automatically delete its own decryptor if it detects a sandbox environment or any other kind of security analysis software on the victims' computers, essentially blowing any chances of regaining access to the victims' files.
The ransomware also comes with a dedicated control panel that allows "clients" to remotely control and monitor attack campaigns. According to Recorded Future researchers, using the control panel would be simple for those that purchase the Karmen ransomware strain as it "requires very minimal technical knowledge".
"For $175, any script kiddie can carry out ransomware attacks," director of advanced collection at Recorded Future, Andrei Barysevich, told ZDNet.
The Karmen ransomware also comes with a "clients" page that allows users to track how many computers have been infected and also provides status updates on any ransom that's been paid. The ransomware features a dashboard that lists information such as how many clients the RaaS has and how much they've racked up in ransom money.
DevBitox has currently sold 20 copies of the Karmen ransomware, leaving only five copies now available for potential buyers. This indicates that the RaaS is profitable.
IBTimes UK has reached out to Recorded Future for further clarity on how the ransomware strain was discovered and the way RaaS models have evolved in the past year. This article will be updated in the event of a response being provided.
RaaS availability on the dark web has seen substantial growth in the recent past, with cybercriminals creating customised malware strains aimed at allowing those with limited technical knowledge to launch attacks. According to a recent analysis by Kaspersky, 75% of ransomware strains that they uncovered were found to have been developed by Russian cybercriminals, indicating the key role they play in the propagation of ransomware.
© Copyright IBTimes 2025. All rights reserved.






















