Tor blocked in Turkey: Here's how to circumvent Tor ban using bridges
Setting up a Tor bridge enables users to access Tor without internet service providers being alerted.

Turkey recently blocked use of both virtual private networks (VPN) and the Tor anonymity network to circumvent internet censorship in the country, which will have a severe impact on citizens' ability to access important information.
In November, the Turkish government asked internet service providers (ISP) to start blocking VPN and Tor, and as of 12 December, Tor restrictions are now confirmed to be in place. A country has the right to dictate its policies, however, the right to access the internet is considered a basic human right by the United Nations, which passed a resolution in June condemning all countries that intentionally prevent or disrupt access to information online.
VPNs are paid services that route internet traffic through a private server so that users can access services in countries where the internet is censored, or to help trick websites into thinking that users are located in a different geographic location.
The Tor anonymity network (named after The Onion Router project) does the same thing, only it anonymises and redirects internet traffic through a worldwide network of relays run by volunteers who set up their computers as Tor exit nodes, so that it becomes impossible to discover where the user is located. Three layers of RSA encryption is added in order to ensure that the source and the final destination of the Tor path is completely anonymised.
It is likely that Turkish ISPs are restricting access to Tor by blocking the IP addresses of Tor exit nodes, which are publicly available and frequently updated. They may also be using deep packet inspection, which is a special box that can inspect each packet of data being sent over the network and make the decision to block all Tor traffic.
However, it is still possible to circumvent Tor blocks by building a "bridge" – a Tor relay not listed in the main Tor directory that comes with pluggable transports to manipulate Tor traffic so that it is not identifiable as a Tor connection, so ISPs can't tell if the traffic comes from Tor.
Join IBTimes UK as we teach you how to set up a Tor bridge:
Step One: Download and update Tor Browser
The first thing you need to do is download the Tor Browser if you haven't already. If you have it on your computer, then start the program and then update it to the latest version in order to make sure you can perform the steps below.
Step Two: Connect via Tor network settings
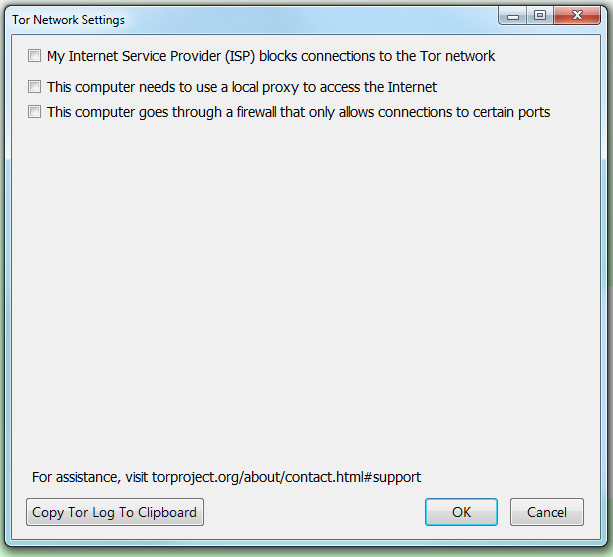
Open the Tor browser, click on the onion icon in the top left-hand corner and then select "Tor Network Settings" from the drop-down menu. Tick the setting that reads 'My Internet Service Provider (ISP) blocks connections to the Tor Network'.
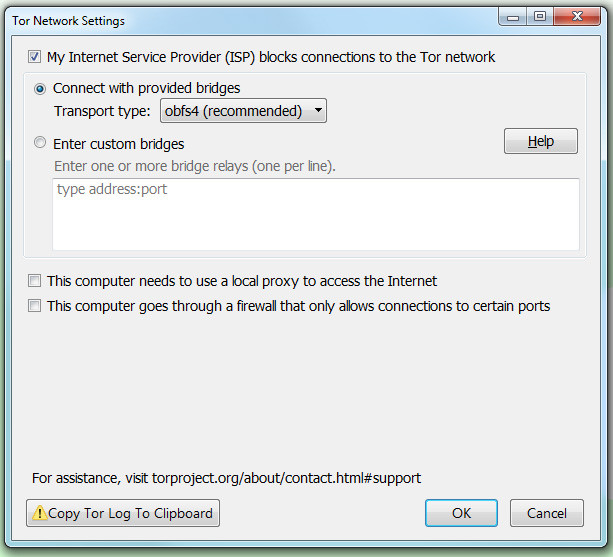
An option will pop up for you to select a bridge from a drop-down menu to connect with. According to independent internet watchdog TurkeyBlocks, obfs4 is working, while obfs3 fails intermittently on some ISPs. Select an option from the drop-down menu, then click OK. If one bridge doesn't work, try another option from the menu.
Step Three: If that doesn't work, go get some bridges
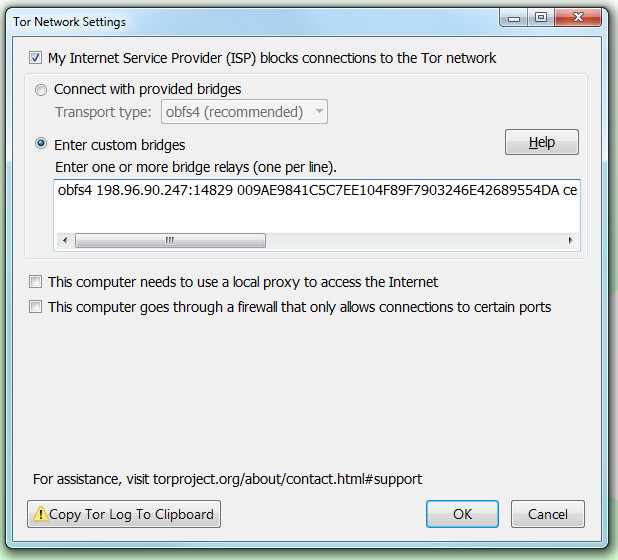
If the Tor Browser is still not able to connect to the internet, then you might need a custom bridge. To get one, go here and look at the Advanced Options box. You will need a pluggable transport to cloak your Tor Bridge. Select an option from the drop-down menu as above, and when you're ready, click 'Get Bridges'.
You should see a list that looks like this:
obfs4 198.96.90.247:14829 009AE9841C5C7EE104F89F7903246E42689554DA cert=4v04LELp0/hnMpzcWxLM0UYEFEp6O0GtHVZYUB/vcflzRI1fDvpOxrqZyuDEqgk+qnVACQ iat-mode=0
obfs4 194.132.209.17:55068 018A09A41B1B5134FFFF908F69CD65CA91625ECC cert=XuBpMmQdIlRiX71utnbVExuHnicns1dH23ev4r/vzlNUhN4tZ0WkNTAzxd2jir35yfpXAQ iat-mode=0
obfs4 194.132.209.214:37610 A974AAC430D8D65DCCAE9B48152DEC31B92F8FAC cert=o1RKMEIS8SzSoMZoBwxZs/Qxvx4bg+Nr5Kk4vsA15BeDgv2uuy5t9Aaah6R6mZdIQaOvaw iat-mode=0
Highlight one relay (one line) from the box, copy it, and then paste it into the 'Enter custom bridges' field and click OK.
You can also choose to email bridges@torproject.org and write 'get transport obfs4' (or whichever pluggable transport you choose) in the body of the email, but you must send the email from Yahoo Mail, Gmail or RiseUp in order to get an automated response, which will look like this:
Hey!
[This is an automated message; please do not reply.]
Here are your bridges:
obfs4 37.218.246.152:34991 22B355C5AAC5F69E46070DBE7544ACCE7957A1B4 cert=hIg+9gYazPkivd50ejP4iNyvEOw/a7dIF08tBknmAm45ClbU5+vYHtYo3COTDJ3RMNQeEw iat-mode=0
obfs4 192.36.31.13:51477 8FDA1F3601535FEFE3BE0457BE5DA7E69CF1B82C cert=YRf/RzlKNzxKm4DTTgdTw0nXn+7r2HZaVROfdqDN/7WdEM9xd+D/jjXoLUhMJhQvCThXKg iat-mode=0
obfs4 174.138.219.97:51987 CCEA79197A59ABCD2BDCAEF796D68654B3C84895 cert=bbMKfqgR3KUHImGQEInuhWOm1hly8jEgDkaDTU9AAVtnp1oC0iw+Jwv/mTXKnTvxn2jFGA iat-mode=0
Step Three: Still not working? Ask for help
If none of the bridges work, email help@rt.torproject.org for support and include as much information about the steps you took to make Tor work, such as which pluggable transports you tried, and which error messages you received from the Tor Browser.
Help run a Tor bridge relay to help others stay connected
Don't have any problems connecting to the internet? That's nice for you. How about helping out? Instead of running a regular Tor node, you could choose to use your server or computer to run a bridge relay. If you only have a tiny bit of bandwidth available, being a bridge will be perfect for you.
Once configured as a bridge relay, your server/computer will not appear in the public Tor network – it will automatically publish its address to the bridge authority, which will give the bridge address out via the two methods listed above.
To do this, edit your Torrc file (the text file containing configuration instructions for how your Tor program should behave), located at Browser > TorBrowser > Data >Tor >torrc inside your Tor Browser directory on Windows. On OS X, right-click the Tor Browser icon and select "Show Package Contents" to view the Tor Browser directory, and then follow the instructions above.
Manually edit the Torrc file so it contains only these four lines:
SocksPort 0
ORPort auto
BridgeRelay 1
Exitpolicy reject *:*
© Copyright IBTimes 2025. All rights reserved.



















