Hacker takes control of Nissan electric vehicle from other side of the world through Leaf app

The Nissan Leaf, one of the world's most popular electric cars, has had a security flaw exposed that allowed a hacker on the other side of the world to take control of its functions and steal information on what journeys it had taken.
Troy Hunt, a security researcher based in Australia, tested out the vulnerability of the Nissan Leaf belonging to a fellow security expert in the UK, and using just the easily-attainable VIN number he was able to turn on the air conditioning and heating systems. Hunt uploaded a video of the hack to YouTube which showed how easy it was for him to execute the process.
Using the Leaf's companion smartphone app NissanConnect, which is used by owners to check up on the vehicle's status like its remaining battery range, Hunt was able to exploit it to turn on the heated seats and climate control, which could cause havoc for prankster hackers who want to run down the battery of an individual's car. It's not as dramatic as the moment remote hackers took control of a moving Jeep, but on a more sinister side it also revealed data about the journeys the Leaf took, which could lead to malicious attackers to use this data to strand individuals.
"Fortunately, the Nissan Leaf doesn't have features like remote unlock or remote start, like some vehicles from other manufacturers do, because that would be a disaster with what's been uncovered. Still, a malicious actor could cause a great deal of problems for owners of the Nissan Leaf," Scott Helm, who assisted Hunt in the hack, said.
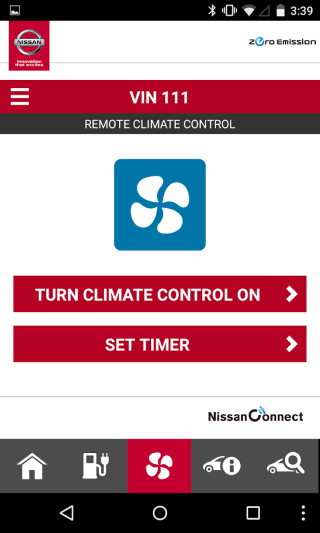
What's more unnerving is how easy it was to do. The Leaf would need to have been connected to the Nissan app and the car has to be stationery but it could still cause chaos and all you need is the VIN, which is clearly displayed on the windscreen of Leaf models.
Security expert Graham Cluley explained: "If hijacking a Jeep remotely was like man landing on the moon, turning a Nissan LEAF owner's air-conditioning on remotely is like walking up the stairs."
How to prevent hackers taking control
However, an easy fix was discovered by simply unregistering the NissanConnect app, which meant Hunt could no longer communicate with the car. Scott Helme provided instructions on how to do this:
"To disable CarWings, owners need to login to the service form their browser, it can't be done through the mobile app. Once logged in, select 'Configuration' from the menu and there is a 'Remove CarWings' button. It appears to be greyed out but the button does work. Once clicked you will receive a prompt to confirm that you wish to disable CarWings and asked to provide a reason why. Click 'Validate' when the appropriate option has been selected and you will get a confirmation message that CarWings has been disabled. You should also receive a confirmation via email."
Hunt claimed he warned Nissan multiple times about the vulnerability since it was discovered on 23 January and it has yet to be fixed. He admits it's not as bad as it could be as it doesn't allow hackers to hijack the driving control but it still allows anyone to manipulate the workings of your vehicle.
© Copyright IBTimes 2025. All rights reserved.




















