LeapFrog: Weak security in 'kid-friendly' tablet could leave children exposed to online snooping
A cybersecurity researcher has slammed the security standards of a "kid-friendly" tablet called the LeapPad Ultra that comes bundled with a vulnerable version of Flash Player. If exploited, the flaw could allow a hacker to monitor a child's online activity, activate the in-built microphone and even take pictures using the front-facing camera on the device.
The tablet in question was released by a firm called LeapFrog that is currently in the process of being acquired by Hong Kong-based toy manufacturer VTech for a hefty $72m ($50m).
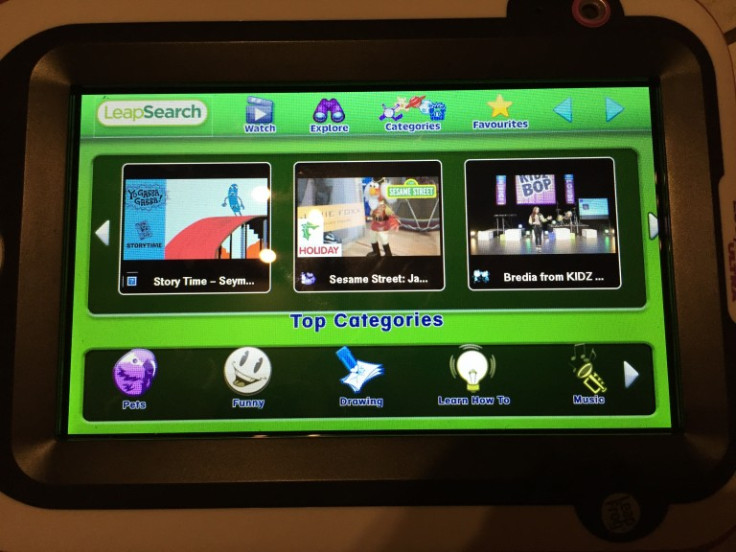
In research outlined on his website, researcher Mike Carthy said he came across a major issue while investigating the tablet's software and web browser. According to Carthy, this browser – which he did note had limited functionality – was serving game and video content to the device via a hard-coded remote web server that was masked from the front-end interface. Unfortunately, this was vulnerable to attack.
"Like any sane security tester – I decided I'd go ahead and load this web address up in my favourite web browser," explained Carthy. "I assumed that LeapFrog would be smart enough to drop HTTP connections from unknown IPs where the client's user-agent didn't match the one on LeapFrog. It turns out I was giving them far too much credit for their effort – since the web page quite happily loaded without restriction."
Flash woes
When Carthy then connected the LeapPad Ultra to his computer a second issue became apparent as the device asked him to update the internal version of Flash Player. With no auto-update feature, this means that, by default, anyone who buys the tablet is running an outdated – and vulnerable – version of this software. Upon analysis, the Flash software on the tablet was 19.0.0.185 which contains a known critical "remote code execution" flaw.

"While it isn't the manufacturer's fault that Adobe Flash is vulnerable – it is their responsibility to make sure their devices install mandatory updates prior to use," Carthy said.
"This particular product only prompted me to update upon connecting it to my computer, something which many parents purchasing these devices may never do [...] what this does highlight is a serious problem with manufacturers not enforcing compulsory updates on products – many of which will have been sitting on shelves for months."
"Full access to the device"
The researcher, who holds a slew of accreditation for his work on cybersecurity and computer testing, added that one of the most concerning findings was an ability to gain "out-of-device" access to the tablet's content server.
"At a minimum this should be locked down by examining the client's user-agent but it should ideally be done using some method of server authentication built into the device," he said. "Can you imagine I'd searched for a persistent XSS vulnerability on that site? I'd be able to inject malicious code into the pages and exploit Adobe Flash, deliver a reverse connection back to my machine and have an international Sesame Street botnet operational within an hour.
"Any malware exploiting these vulnerabilities would be able to gain full access to the device – allowing an attacker activate the built-in microphone, monitor your child's activity and even take pictures of them using both the front and rear facing cameras on the device. Yes, you read that sentence correctly."
Carthy said his research is a "fairly devastating assessment" for a device that claims to be "kid-safe". "LeapFrog need to tighten up their content server with mandatory authentication, enforce compulsory updates upon initial device configuration and ditch Adobe Flash for their video content entirely," he concluded.
In response to the claims, a spokesperson for LeapFrog told IBTimes UK: "We would like to reassure you that LeapFrog takes the security of consumer information very seriously and have appropriate measures in place to ensure that any information we retain to provide a great experience for our products remains safe and secure. Consumer security and trust is of the upmost importance to us and we are looking into this as a matter of urgency."
Potential parent company VTech recently encountered its own problems with cybersecurity after a hack on its systems resulted in the loss of over six million parent and child records including chat logs, audio files and even stored photographs.
© Copyright IBTimes 2025. All rights reserved.




















