Quantum cryptography breakthrough: 'Unbreakable security' possible using pulse laser seeding
Computer scientists and engineers from Cambridge University and Toshiba have devised a new laser-based system that speeds up the rate at which data is securely transmitted to 1Mbps, paving the way for impossible-to-break quantum cryptography.
Although quantum computers are still only a concept, many computer scientists believe that the super-powerful computers will be available within the next 50 years, and that they will be able to solve extremely large numbers quickly, using quantum computing algorithms, such as Shor's factoring algorithm .
While solving large prime numbers quickly would mean computers could perform tasks much faster, it also means that quantum computers would find it easy to break current encryption methods, which rely on complex mathematical problems.
The National Security Agency (NSA) in the US is deeply afraid that current security cryptography used to protect almost all electronic data over the past 50 years will easily be unravelled by hackers once quantum computers become a reality, and to that end, has been advising US businesses to start investing in quantum-resistant algorithms since August 2015.
Quantum cryptography and the One-time pad
To combat this problem, in recent years researchers have been working to develop quantum cryptography, whereby information is stored and hidden within photons (particles of light) emitted from lasers, using the only existing mathematically unbreakable encryption in the world – the One-time pad (OTP).
The OTP, also known as the "Vernam-cipher" or the "perfect cipher", was first conceptualised in 1882 by Frank Miller, and then patented by Gilbert S Vernam in 1919. It is a crypto algorithm whereby plaintext is combined with a random secret key.
The plaintext message that needs to be hidden is encrypted by combining every single character of the message with a corresponding bit or character from the OTP. As long as the secret key is truly random and the plaintext message is never reused in whole or in part, and is kept secret, then the encrypted cipher text is absolutely impossible to decrypt.
While the technology does work, the secret key has to be as long as the plaintext message that needs to be hidden, and it can only transmit the data very slowly at the rate of only a few hundred bits per second. But if quantum mechanics is added into the mix, the secret key used in OTP will change whenever an attacker tries to intercept the message, and since it was first proposed in the 1980s, researchers have been trying to make it work as a usable real-world system.
Changing the way quantum cryptography works
In existing systems, information is hidden in photons emitted from lasers. For example, Alice sends a secret key via polarised photons in different directions. The receiver of the message, Bob, uses photon detectors to measure in which direction the photons are being polarised, and the detectors translate the photons into bits in order to give Bob the correct secret key to decrypt the message.
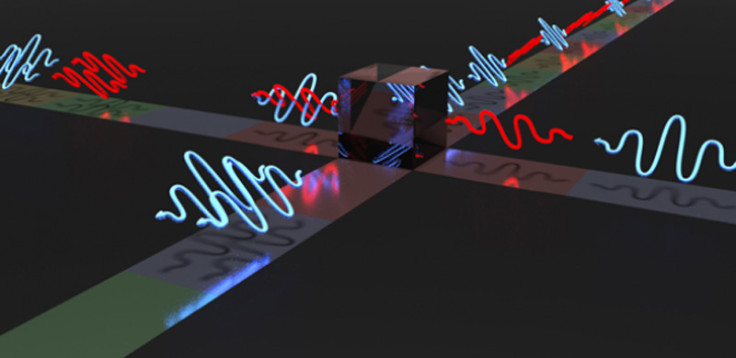
The researchers have developed a new quantum cryptography protocol called measurement-device-independent quantum key distribution (MDI-QKD), which changes the way the messages are sent. So instead of Alice and Bob both needing to have a photon detector to work out the message, the photons are instead sent to a central node.
The central node allows the photons to pass through a laser beam splitter and measures them, and the resulting information discloses only the correlation between the different bits, but not their exact values, which stay secret.
Transmitting information 10 times faster than ever before
But now, the researchers from Cambridge University and Toshiba Research Europe have succeeded in using a technique called pulsed laser seeding to get information to transmit at rates that are over 10 times faster than any previous attempts.
To make MDI-QKD work at the moment, laser pulses used to measure the photons have to be long, which means information transmission rates are restricted to only a few hundred bits per second (bps) or less. By using pulse laser seeding, the amount of "time jitter" in the pulses is reduced, meaning that much shorter pulses can be used, and information can be transmitted at rates as high as 1Mbps.
"In theory, the attacker could have all of the power possible under the laws of physics, but they still wouldn't be able to crack the code," said the paper's first author Lucian Comandar, a PhD student at Cambridge's Department of Engineering and Toshiba's Cambridge Research Laboratory.
"This protocol gives us the highest possible degree of security at very high clock rates. It could point the way to a practical implementation of quantum cryptography."
The research, entitled Quantum Key Distribution Without Detector Vulnerabilities Using Optically Seeded Lasers is published in the journal Nature Photonics.
© Copyright IBTimes 2025. All rights reserved.





















