Flame Virus: How to Check if You Are Infected With Malware
Kaspersky Lab has taken a look at the code for the Flame Virus and has started to map some of the qualities of this malicious malware.
Using the information collected so far it is possible to find out if a computer has been infected.
"The main module of Flame is a DLL file called mssecmgr.ocx," Alexander Gostev, chief security expert at Kaspersky Lab, revealed in a blog post.
"We've discovered two modifications of this module. Most of the infected machines contained its 'big' version, 6Mb in size, and carrying and deploying additional modules. The smaller version's size is only 900Kb and contains no additional modules. After installation, the small module connects to one of the C&C servers and tries to download and install the remaining components from there."
Gostev said the Mssecmgr file may be called different names on infected machines, depending on the method of infection and the current internal state of the malware (installation, replication, upgrade). For example, it could be called wavesup3.drv, ~zff042.ocx or msdclr64.ocx.
The analysis means users can perform a quick manual check of their computer systems for presence of a Flame infection.
Step 1
Perform a search for the file ~DEB93D.tmp. Its presence on a system means that it either is or has been infected by Flame.
Step 2
Check the registry key HKLM_SYSTEMCurrentControlSetControlLsa Authentication Packages. If you find mssecmgr.ocx or authpack.ocx in there - you are infected with Flame.
Step 3
Check for the presence of the following catalogues. If they are present - you are infected.
C:Program FilesCommon FilesMicrosoft SharedMSSecurityMgr
C:Program FilesCommon FilesMicrosoft SharedMSAudio
C:Program FilesCommon FilesMicrosoft SharedMSAuthCtrl
C:Program FilesCommon FilesMicrosoft SharedMSAPackages
C:Program FilesCommon FilesMicrosoft SharedMSSndMix
Step 4
Conduct a search for the rest of the filenames listed below. All of them are unique and if they are discovered there is a strong possibility of a Flame Virus infection.
mssecmgr.ocx
advnetcfg.ocx
msglu32.ocx
nteps32.ocx
soapr32.ocx
ccalc32.sys
boot32drv.sys
~DEB93D.tmp
~8C5FF6C.tmp
~DF05AC8.tmp
~DFD85D3.tmp
~DFL*.tmp
~dra*.tmp
~fghz.tmp
~HLV*.tmp
~KWI988.tmp
~KWI989.tmp
~rei524.tmp
~rei525.tmp
~rf288.tmp
~rft374.tmp
~TFL848.tmp
~TFL849.tmp
~mso2a0.tmp
~mso2a1.tmp
~mso2a2.tmp
sstab*.dat
dstrlog.dat
lmcache.dat
mscrypt.dat
wpgfilter.dat
ntcache.dat
rccache.dat
audfilter.dat
ssitable
audache
secindex.dat
wavesup3.drv
svchost1ex.mof
Svchostevt.mof
frog.bat
netcfgi.ocx
authpack.ocx
~a29.tmp
rdcvlt32.exe
to961.tmp
authcfg.dat
Wpab32.bat
ctrllist.dat
winrt32.ocx
winrt32.dll
scsec32.exe
grb9m2.bat
winconf32.ocx
watchxb.sys
sdclt32.exe
scaud32.exe
pcldrvx.ocx
mssvc32.ocx
mssui.drv
modevga.com
indsvc32.ocx
comspol32.ocx
comspol32.dll
browse32.ocx
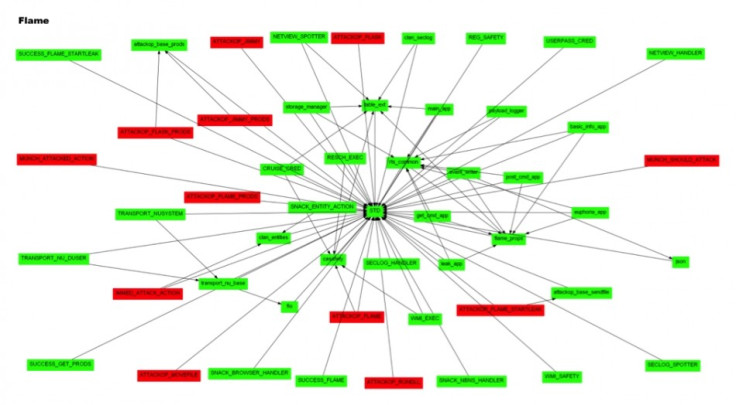
Kaspersky Lab's detailed look at the functionality of the malware shows that it contains a number of different elements, all with specific jobs.
For example, the Beetlejuice unit can use Bluetooth to turn your computer into a 'beacon' and announces it as a discoverable device. Meanwhile, the Weasel unit creates a directory listing of the infected computer.
Below is a brief overview of the available units. The names were extracted from the binary and the 146 resource.
Beetlejuice
Bluetooth: enumerates devices around the infected machine.
May turn itself into a "beacon": announces the computer as a discoverable device and encode the status of the malware in device information using base64.
Microbe
Records audio from existing hardware sources. Lists all multimedia devices, stores complete device configuration, tries to select suitable recording device.
Infectmedia
Selects one of the methods for infecting media, i.e. USB disks. Available methods: Autorun_infector, Euphoria.
Autorun_infector
Creates "autorun.inf" that contains the malware and starts with a custom "open" command. The same method was used by Stuxnet before it employed the LNK exploit.
Euphoria
Create a "junction point" directory with "desktop.ini" and "target.lnk" from LINK1 and LINK2 entries of resource 146 (were not present in the resource file). The directory acts as a shortcut for launching Flame.
Limbo
Creates backdoor accounts with login "HelpAssistant" on the machines within the network domain if appropriate rights are available.
Frog
Infect machines using pre-defined user accounts. The only user account specified in the configuration resource is "HelpAssistant" that is created by the "Limbo" attack.
Munch
HTTP server that responds to "/view.php" and "/wpad.dat" requests.
Snack
Listens on network interfaces, receives and saves NBNS packets in a log file. Has an option to start only when "Munch" is started. Collected data is then used for replicating by network.
Boot_dll_loader
Configuration section that contains the list of all additional modules that should be loaded and started.
Weasel
Creates a directory listing of the infected computer.
Boost
Creates a list of "interesting" files using several filename masks.
Telemetry
Logging facilities
Gator
When an Internet connection becomes available, it connects to the C&C servers, downloads new modules, and uploads collected data.
Security
Identifies programs that may be hazardous to Flame, i.e., anti-virus programs and firewalls.
Bunny, Dbquery, Driller, Headache and Gadget
The purpose of these modules is not yet known.
© Copyright IBTimes 2025. All rights reserved.





















