How to fix virtual machine error with TaiG jailbreak 2.1.1

Chinese jailbreak developer team, TaiG, has just confirmed via its official Weibo account that the TaiG 2.1.0 and 2.1.1 jailbreak packages have been leaked through unofficial sources, while the internet is abuzz with fresh set of issues including the virtual machine error with leaked TaiG jailbreak 2.1.1.
Here is the official statement from TaiG (Google Translated):
Fellow users, circulated on the Internet today, the new installation package some TaiG, TaiG beta package or false package, not the official version, tai chi currently only officially released the official version V2.0.0 jailbreak tool. Please be patient, we will release the new version as soon as possible and the first time in the microblogging to inform you. Sorry to keep you waiting.
Suggest that you do not download the beta package spread out, because there are application icon missing bug, the official version will be fixed. We are working with Saurik (Cydia Author) UI cache solve problems, solutions complete the new version can be released.
Meanwhile, folks at iDownloadBlog have already secured a fix for this virtual machine issue through reader Mohamed Elkady, who has shared an interesting tiny trick to bypass this error.
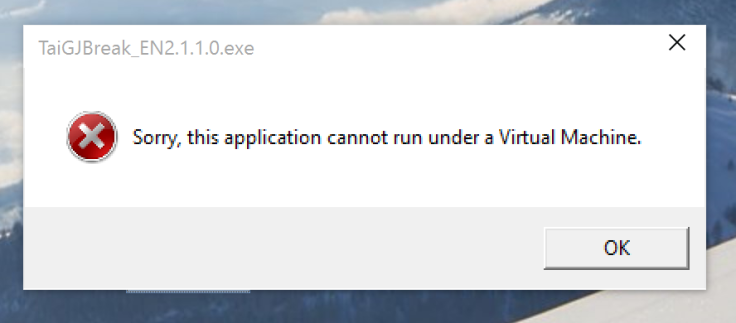
Here is the complete step-by-step guide for installing the fix on iOS 8.3 devices running the TaiG jailbreak with VMware Fusion 7 installed:
Step 1: Power off your computer running virtual machine completely
Step 2: Navigate to the virtual machine folder in ~/Documents/Virtual Machines/ directory
Step 3: Right-click on the empty space inside the folder on your virtual machine and select Show Package Contents
Step 4: Locate the file that ends with .vmx file extension
Step 5: Right-click > choose Open With and select TextEdit
Step 6: Scroll to the bottom of the file and paste the following on a new line:
monitor_control.restrict_backdoor = "true"
Step 7: Save the file
Step 8: Launch your virtual machine
Step 9: Once again run the TaiG jailbreak tool and the issue must be fixed
For further assistance, check out the video tutorial below:
[Source: iDownloadBlog]
© Copyright IBTimes 2025. All rights reserved.



















