Kash Patel Email Leak Explained: What Was Revealed, Possible Motive and What Happens Next
A decade of Kash Patel's digital life, hauled into the open by Iran-linked hackers, shows how personal inboxes have quietly become the soft underbelly of modern politics.

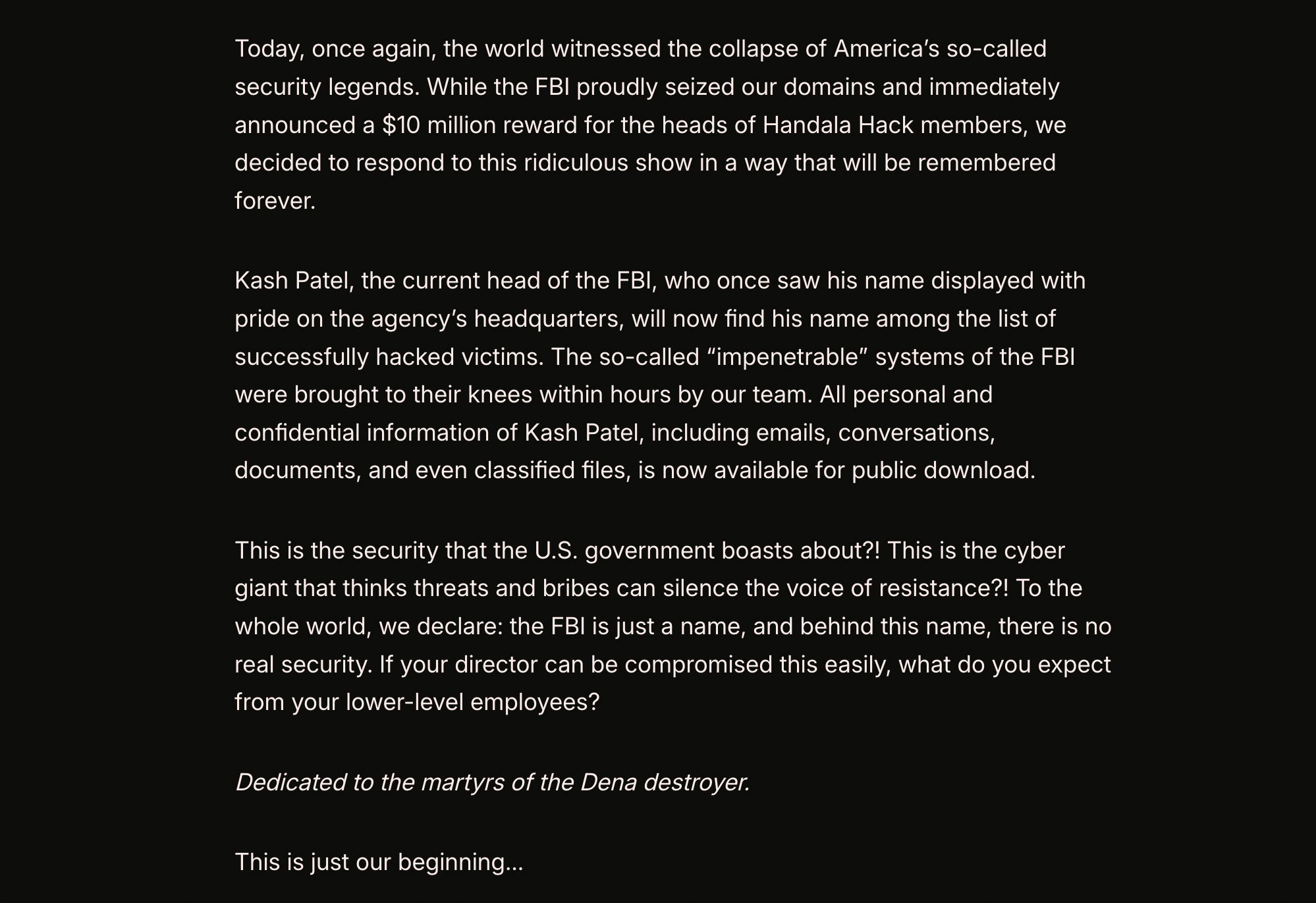
Iran-linked hackers have broken into the personal email account of former US national security official Kash Patel, leaking more than 300 emails and a trove of personal photos online, according to the FBI and material reviewed by Reuters this week. The cache, published by a group calling itself Handala Hack Team, includes years of correspondence and images apparently intended to embarrass Patel rather than expose state secrets.
For starters, Kash Patel is a former senior aide in Donald Trump's White House and at the Pentagon, and a prominent pro-Trump media figure since leaving government. His name and a matching Gmail address had surfaced in earlier data breaches, but this is the first time hackers openly claim to have rifled through his inbox and curated the contents for public release. The FBI has confirmed the breach, while stressing that the compromised data is 'historical in nature' and does not involve government systems or classified material.
Inside The Kash Patel Email Leak
The Kash Patel files posted by Handala include a sample of more than 300 emails, reportedly spanning the period from 2010 to 2019. Reuters, which examined the dataset, said the messages appear to combine personal and work-related exchanges, though the agency underlined that it could not independently verify the authenticity of each email.
Alongside the correspondence, the hackers published a gallery of personal photographs of Patel. The images show him smoking cigars, riding in a vintage convertible and posing casually, far from the buttoned-up world of Capitol Hill hearing rooms and secure briefings. None of this is illegal or especially unusual, but releasing such material en masse is a well-worn tactic in the hacking playbook: turn a private life into public spectacle and let the discomfort do the rest.
🚨 BREAKING: Iran-linked hacking group Handala claims it breached FBI Director Kash Patel’s personal email—and leaked photos and documents online.
— Brian Allen (@allenanalysis) March 27, 2026
DOJ confirms:
His email was compromised. Some of the leaked material appears to include
personal and professional correspondence.… pic.twitter.com/9oYuJVhqiS
Dark web intelligence firm District 4 Labs told Reuters that the account targeted appears to match a Gmail address linked to Patel in previous credential leaks. That detail matters, because it hints at a familiar weakness rather than any elite spycraft: once an email address and password combination is floating around in criminal markets, it can be tried again and again until someone gets lucky or the victim changes it.
The FBI, keen to cool speculation that the incident posed a live security threat, said through spokesperson Ben Williamson that investigators had taken 'all necessary steps' to mitigate risks. The material, Williamson added, was old and did not touch government networks or national security systems.
The Iranian state-backed “Handala Hack Team” is claiming to have breached FBI Director Kash Patel’s personal email, posting an apparent resume and several old photos of Patel. pic.twitter.com/PHwkBrw88z
— OSINTdefender (@sentdefender) March 27, 2026
Why Kash Patel Was In The Crosshairs
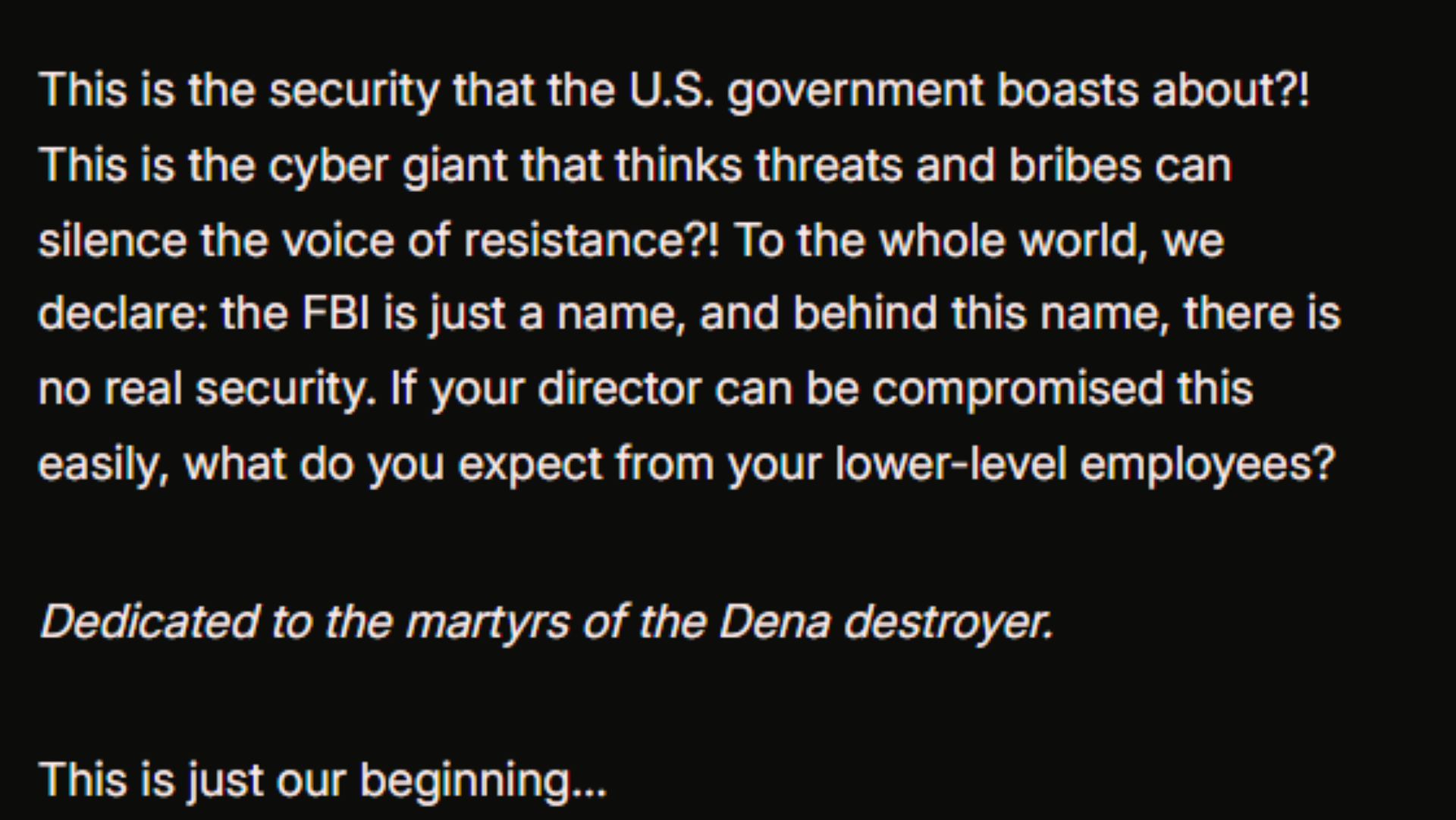
The group claiming responsibility for the Kash Patel email leak, Handala Hack Team, presents itself publicly as a pro-Palestinian hacktivist outfit. Western cyber researchers, cited by Reuters, are more sceptical. They see Handala as one of several brands used by Iranian cyberintelligence units to mask state direction behind the posture of grass-roots activism.
In recent months, Handala has claimed cyberattacks on US-based medical company Stryker and said it leaked data connected to Lockheed Martin employees in the Middle East. Some of those boasts remain unverified, but they sketch a pattern: politically symbolic targets, mostly American, chosen for their visibility as much as their technical value.
🚨‼️ BREAKING: FBI Director Kash Patel's Gmail account was hacked
— International Cyber Digest (@IntCyberDigest) March 27, 2026
by Iranian nation-state hackers.
They have published his entire inbox, including mails on his home in India, private life, personal data, business dealings and travel history (Havana, Cuba!). pic.twitter.com/stYtjklOyU
Kash Patel fits that pattern. He is a vocal critic of the FBI and US intelligence agencies, a public defender of Donald Trump and a recognisable face in conservative media. For Iranian-linked actors seeking both headlines and a pressure point on Washington, he is a low-cost, high-profile target.
Gil Messing, chief of staff at Israeli cybersecurity firm Check Point, told Reuters that the Patel operation appears part of a broader play to unsettle US officials and former officials by poking at their private lives. The aim, he suggested, is to 'make them feel vulnerable' and to send the message that no inbox is off limits.
Yesterday Handala published the names of multiple US citizens working for Lockheed Martin in israel.
— Daniel Delgado (@DelgadoLegend) March 27, 2026
The FBI then seized the domain of Handala.
Today Handala published an old hacked Gmail Account of Kash Patel with all sort of personal e-mails, videos and images in response. https://t.co/8TWFy8MtlW pic.twitter.com/2kmsWSmrU3
That reading echoes a recent US intelligence assessment, also reported by Reuters, which predicted that Iran and allied groups may favour relatively low-level but noisy cyber operations, such as email and data breaches, as a way to retaliate for US and Israeli actions without crossing the threshold into more destructive attacks.
What The Kash Patel Hack Tells Us About Personal Email Risk
If any of this feels familiar, that is because it is. Senior figures' personal accounts have been soft targets for years. In 2016, the Gmail of Democratic strategist John Podesta was hacked via a phishing email, feeding a steady drip of disclosures into the US presidential race. A year earlier, then-CIA director John Brennan's private email was breached by a teenager using social engineering tricks rather than sophisticated malware.
The Kash Patel breach sits squarely in that tradition. Personal accounts are often less protected than official ones, yet they can hold years of contacts, calendars, attachments and conversations. Even when nothing is classified, the material can be mined for embarrassment, context or leverage.
🤦 HUMILIATING EXPOSURE: 🇺🇸 KASH PATEL PHOTOS LEAKED
— RAJAT (@RajatJain) March 27, 2026
Iran-linked hackers compromised FBI Director Kash Patel’s personal email and released private photos plus old documents.
• Handala Hack Team took credit for the breach
• Photos include Patel posing with cigar and rum
•… pic.twitter.com/SRIh8pD0QR
Analysts note that these attacks rarely require elite technical skills. They can hinge on password reuse, weak recovery questions or old credentials resurfacing from unrelated data dumps. But once inside, the attacker has something far more valuable than a one-off document: a story to tell about their target's life, past associations and habits.
In Patel's case, nothing in the public portion of the leak suggests that state secrets were sitting in his Gmail, and officials are adamant that no classified information has been compromised. It is not yet clear whether the hackers are holding back additional data or exaggerating what they obtained, a common tactic to stretch the news cycle.
© Copyright IBTimes 2025. All rights reserved.






















